What Is IT Mapping?
Today’s organizations operate in a hybrid multi-cloud and virtualized world. The ability to do IT mapping of infrastructure and application dependencies on-premises and in the cloud is the foundation of many business processes. These include incident management, documenting and managing IT assets, cloud migration, data center transformation, business continuity and disaster recovery, and cybersecurity and microsegmentation.
IT infrastructure mapping builds a map that provides a visualization of a network’s topology and structure. It is highly useful for understanding both the physical and logical layout of a network, seeing the relationships between devices and applications, and identifying problems or opportunities for optimization. An IT infrastructure map is often the best way to troubleshoot complex issues involving hardware and software on a network.
An IT infrastructure map is a detailed diagram that illustrates which servers, applications, and other endpoints are deployed on the network and the network equipment that manages traffic such as routers, firewalls, and ports.
Every digital organization now needs a comprehensive (all environments), real-time, fast, and repeatable application dependency mapping tool that doesn’t affect performance. (For more information, see The Complete Guide to Application Mapping.)
This is part of an extensive series of guides about information security
Table of Contents
ToggleBenefits of IT Mapping
Enhanced Visibility
One of the primary benefits of IT mapping is that it enhances visibility into your IT infrastructure. With a comprehensive map, you can see exactly what assets you have, where they are, how they’re connected, and how they’re being used.
Related content: Read our guide to network microsegmentation
This improved visibility leads to a better understanding of your IT landscape. You can see how changes in one area might impact other areas, identify potential bottlenecks or vulnerabilities, and make more informed decisions about your IT strategy.
Better Risk Management
Another key benefit of IT mapping is enhanced risk management. By providing a comprehensive view of your IT landscape, an IT map can help you identify potential risks and vulnerabilities.
For instance, you might identify a critical server that’s running outdated software, a network connection that’s not properly secured, or a database that’s not being regularly backed up. By identifying these risks, you can take proactive steps to mitigate them before they lead to a major incident.
Related content: Read our guide to network mapping tools
Improved IT Governance
IT mapping also plays a crucial role in IT governance. By providing a clear picture of your IT landscape, it can help you establish and enforce IT policies and procedures.
For example, you might use your IT map to define what software is allowed on your network, what hardware configurations are acceptable, and what security measures need to be in place. You can also use it to track compliance with these policies, identify any deviations, and take corrective action as needed.
Learn more in our detailed guide to microsegmentation beginners guide
An IT map can also support strategic planning. By understanding your current IT landscape, you can make more informed decisions about future investments, identify areas for improvement, and align your IT strategy with your overall business goals.
Performance Optimization
Finally, IT mapping can help optimize the performance of your IT infrastructure. By understanding how your IT assets are connected and how they’re being used, you can identify opportunities for optimization.
This might involve consolidating servers, reconfiguring networks, updating software, or other steps to improve efficiency and performance. Moreover, by tracking changes over time, you can measure the impact of these optimizations and continuously refine your approach.

Lanir specializes in founding new tech companies for Enterprise Software: Assemble and nurture a great team, Early stage funding to growth late stage, One design partner to hundreds of enterprise customers, MVP to Enterprise grade product, Low level kernel engineering to AI/ML and BigData, One advisory board to a long list of shareholders and board members of the worlds largest VCs
Tips from the Expert
In my experience, here are tips that can help you better leverage IT mapping:
- Automate asset discovery Utilize automation tools to regularly scan and update your asset inventory. This ensures your map reflects real-time changes and reduces the risk of human error.
- Integrate with CI/CD pipelines Link your IT mapping tools with your Continuous Integration/Continuous Deployment (CI/CD) pipelines to automatically update dependencies as new applications and services are deployed.
- Leverage AI and ML for insights Implement AI and ML to analyze your IT map for patterns and predictive maintenance. These technologies can help you anticipate failures and optimize performance proactively.
- Establish clear data governance policies Define and enforce strict data governance policies to ensure that all mapped data is accurate, secure, and compliant with regulatory standards.
- Conduct regular dependency audits Periodically audit application dependencies to ensure they are still valid. This helps in maintaining an accurate map and avoiding potential disruptions due to broken dependencies.
How IT Mapping Works
IT mapping is a process that involves creating a visual representation of an organization’s IT infrastructure, including hardware, software, applications, and data flows. Here are the steps involved in how IT mapping works:
1. Inventory assets: The first step in IT mapping is to inventory all IT assets, including hardware devices, software applications, and data sources. This includes identifying the location, specification, and configuration of each asset.
2. Identify relationships: Once the inventory is complete, the relationships between IT assets must be identified. This includes data flows, connections, and dependencies between different parts of the system.
Related content: Read our guide to IT system mapping
3. Create visualizations: With the assets and relationships identified, the IT environment can be visualized using diagrams or other visual representations. This includes depicting hardware and software components, data flows, and connections between different parts of the system.
4. Document details: The IT mapping process also involves documenting the IT environment, including specifications, configurations, and other important details about each asset. This documentation can be used for reference and to support IT decision-making.
Learn more in our detailed guide to check SSL certificates
5. Analyze and optimize: With the IT environment documented and visualized, it is possible to analyze the infrastructure to identify areas for optimization or improvement. This includes identifying inefficiencies, redundancies, or security vulnerabilities. Based on the analysis, IT mapping can inform IT planning and decision-making.
6. Update and maintain: IT mapping is an ongoing process that requires updating and maintenance to remain accurate and relevant. As the IT environment evolves, IT mapping must be updated to reflect changes in hardware, software, and data flows.
IT Mapping Challenges for Digital Organizations
IT infrastructure and application mapping is a process for discovering and understanding every application and device, along with their dependencies and services across an organization’s entire digital footprint. With a basic understanding of the broad nature of application dependency mapping, organizations can look at these challenges within and across all environments.
Cloud Migration
Nearly every organization has some applications and workloads in the cloud or has upcoming plans in place to do so. According to Nutanix research, 91% of surveyed enterprises migrated at least one application in the last year.
Learn more in our detailed guide to vmware aria operations for networks
On-premises and cloud applications will need to maintain their dependencies to databases, workloads, and other applications after a migration to avoid scenarios where they stop working. The lack of proper application dependency mapping can lead to the disruption or breaking of these dependencies, which can exist across bare metal, virtual servers, and cloud providers, in any migration process. These needs make it vital to have a clear view of every dependency when planning and executing a migration.
Related content: Read our guide to network visibility
Disaster Recovery and Microsegmentation
BCDR strategies keep an organization operational in the wake of cybersecurity attacks that get inside the network (such as ransomware) or natural disasters. This approach is often a major reason for cloud migration and data center transformation (via a hybrid-cloud model mix of on-premises and cloud).
An organization must identify all dependencies and migrate them together to ensure proper disaster recovery. If not, the whole point of backups is moot since they lose ongoing application updates and dependencies without ongoing application mapping.
Microsegmentation is an important way to protect the network from attacks by separating environments, applications, workloads, VMs, and users to apply least privilege access policies to data/workflows based on compliance needs. Without a clear understanding of application and IT infrastructure using comprehensive mapping, it becomes impossible to protect these different areas, applications, and workflows.
Related content: Read our guide to microsegmentation guide
Data Center Transformation
Organizations can easily lose track of dependencies between applications, devices, and IT infrastructure that grows in complexity inside their data center, the cloud, and beyond the network’s edge. These environments and connections are changing daily in the modern organization where IT documentation and assessment are critical to keeping data, devices, applications, and workflows moving and secure.
While there are several methods that organizations have historically used to map applications and IT infrastructure, they all have their pros and cons. To understand why they each may have blind spots that make comprehensive and real-time mapping challenging, it’s best to start by looking at the different approaches in use today.
Application Mapping Approaches: Pros and Cons
Since the emergence of ITSM and ITAM, organizations have understood how imperative it is to keep track of IT infrastructure, devices, applications, services, and their dependencies.
1. Cloud Provider and IT Mapping Tools
Even in the current cloud era, which is always changing, the three largest providers—AWS, GCP, and Azure—all have service discovery tools for mapping application resources.
Pros
These tools can play a vital role in understanding the state of all cloud resources to help limit cloud spend, improve developer productivity, and increase application availability among others.
Cons
In a hybrid multi-cloud world, underlying dependencies can stretch across on-premises data centers and multiple clouds and providers. These mapping tools can often be relegated to silos (by design) that prevent a holistic view and create unmanageable complexity in the mapping process.
Related content: Read our guide to snmp
2. CMDB Mapping
There are many types and configurations of the configuration management database (CMDB) in use across countless organizations. It ideally acts as a repository for storing all information and dependencies related to all IT assets, which are known as configuration items (CI). CIs include hardware, devices, software, and networks, along with their performance, configuration, location, financial, licensing, and maintenance data.
Pros
When a CMDB provides a complete picture of an organization’s assets, it helps the business make better IT decisions through problem resolution, incident response, and updates for networks and infrastructure. Other benefits include planning for business strategy, budgets, and regulatory compliance. The primary challenge with a CMDB is keeping it updated. This plays out in many ways that limit the CMDB as a single source of truth for IT assets across every environment.
Cons
Most IT teams struggle to maintain an accurate CMDB for a variety of reasons, but mostly because IT environments on-premises and in the cloud are constantly changing. Many CMDBs cannot respond to the pace of DevOps or virtual assets like VMs, containers, and other cloud application resources. Others still require manual data entry validation and manual audits to stay up to date with new CI configurations and dependency changes.
Related content: Read our guide to check ssl certificates
Although modern CMBDs include application mapping, they often only collect data based on a specific request. They also can have limited ability to see all changes in dependencies and services and provide root cause analysis within that request. This leads to a limited snapshot-in-time view of an application and some of its dependencies without providing the ability to see if it’s operating correctly and delivering the required service level.
3. Application Performance Management (APM)
APM provides real-time application performance monitoring across an organization’s application portfolio. APM enables a view into service level agreement compliance, performance level, and user challenge identification.
Pros
An APM solution’s diagnostics should give administrators insights into problems within the application stack to plan proactive remediation. These real-time performance alerts and reports generated by the APM are vital to maximizing business revenue, continuity, efficient operation, cost reductions, and end-user experience.
Cons
APM tools require the installation of an agent for targeted infrastructure or applications. The result is that organizations cannot effectively use these tools with new applications and VMs that are spun up and down, or third-party enterprise applications like SAP, as just one example.
The agent-based nature of APM tools creates silos, with gaps in data on application efficiencies across environments, including on-premises and the cloud or multi-cloud. This makes it impossible to see real-time application performance with detailed knowledge across dependencies, in turn making root cause analysis nearly impossible.
4. Application Dependency Mapping (ADM)
The Application Dependency Mapping (ADM) process identifies all IT and application elements and services across an organization’s IT environment. ADM provides a means of seeing how these elements work together and individually in real time to assess health and proactively make improvements. Most ADM tools work without agents and use various methods for finding application dependencies in real time. This supports the dynamic nature of application development where applications and infrastructure can change daily.
Pros
The right ADM tool can provide the most combined benefits of the solutions covered in this blog. CMDBs currently exist and serve ongoing and unique purposes in many organizations, and some organizations already have an existing APM. In these cases, the ideal ADM can work with these solutions and a world of third-party tools in the enterprise.
Cons
As a mapping tool category, ADM has few downsides, but many of these tools fall short in their ability to provide real-time, repeatable, and comprehensive mapping across environments. The different approaches used by ADM solution providers can deliver different results based on a narrower basis for environment mapping.
This can lead to an incomplete picture of the entire IT infrastructure, its applications, and their dependencies where environmental changes are continuous. The ideal scenario is an ADM tool that captures the state and relationships of all assets across every environment in real time without slowing performance via easily repeatable passive scanning.
Notable IT Mapping Tools
Application Dependency Mapping (ADM) and Observability Tools
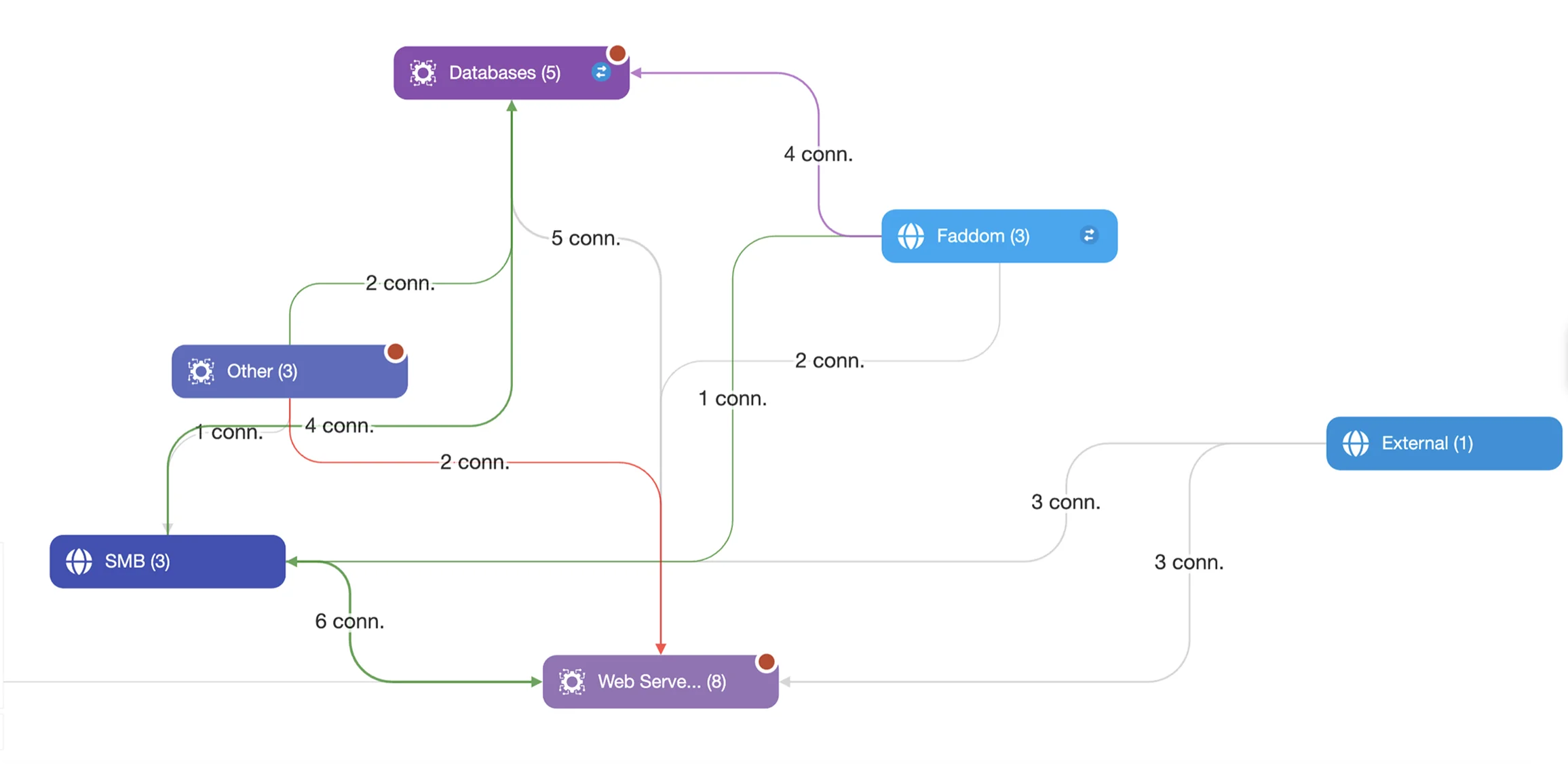
1. Faddom
Faddom is an agentless application dependency mapping (ADM) platform that provides real-time visibility into complex hybrid environments. It continuously discovers servers, applications, and their true dependencies across on-premises, cloud and hybrid infrastructure, creating a live operational view of how everything actually communicates. This enables IT, Cloud, and Security teams to work from a single, accurate source of truth when managing assets, planning changes, or responding to incidents.
Key features:
- Real-time dependency mapping: Visualizes how applications, services, and infrastructure interact across environments to support troubleshooting, change planning, and risk analysis.
- Agentless, continuous discovery: Uses passive traffic analysis to automatically discover assets and relationships without agents, credentials, or performance impact.
- Hybrid environment visibility: Maps dependencies across on-prem, cloud, containers, and virtualized environments in one unified view.
- CMDB enrichment and accuracy: Integrates with platforms like ServiceNow to keep configuration data and relationships continuously updated and reliable.
- Change and migration confidence: Helps teams understand impact and avoid disruptions when performing migrations, transformations, or infrastructure changes.
- Security and microsegmentation support: Identifies traffic flows and hidden connections to strengthen segmentation strategies and reduce attack surfaces.
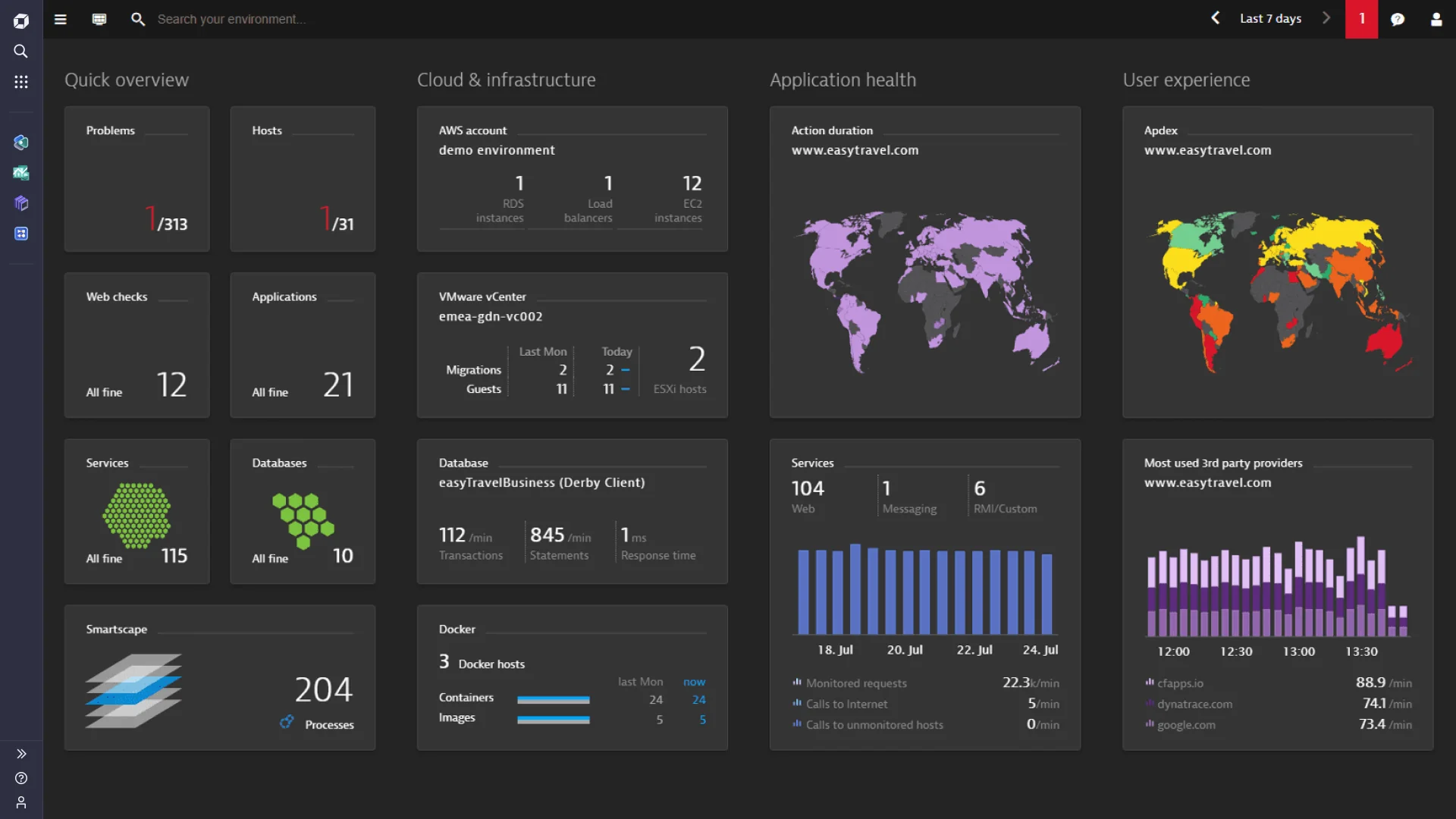
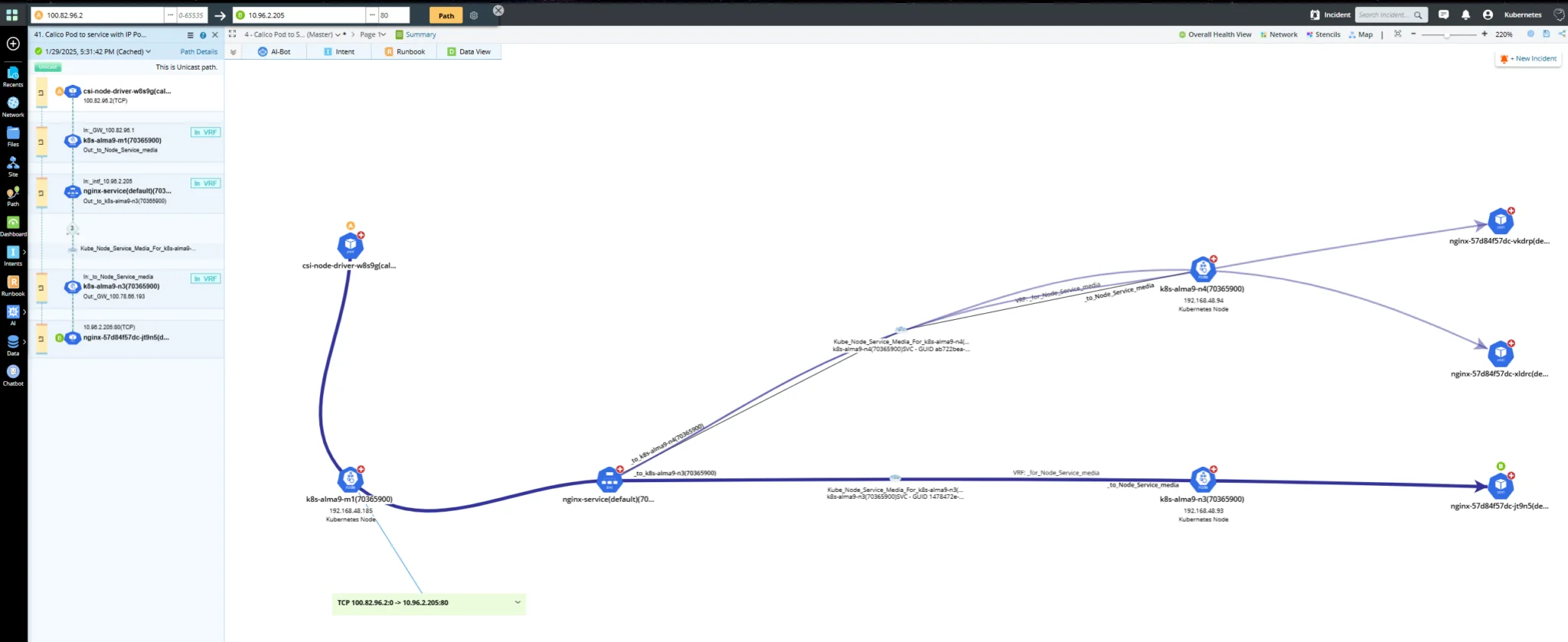
2. Dynatrace
Dynatrace is an observability platform that combines application, infrastructure, and security monitoring with AI-driven analysis. It collects and correlates data across environments to provide real-time insights into system behavior and dependencies. Its focus is on connecting data across the full stack and using automation to detect issues and identify root causes.
Key features:
- Full-stack observability: Monitors applications, infrastructure, and user experience across environments in a unified platform
- AI-driven insights: Uses deterministic AI for anomaly detection, prediction, and root cause analysis
- Real-time data analysis: Processes and analyzes data continuously for immediate visibility into system state
- Automation capabilities: Automates workflows and operational tasks to reduce manual intervention
- Broad integrations: Supports integration with major cloud platforms and enterprise technologies
Source: Dynatrace
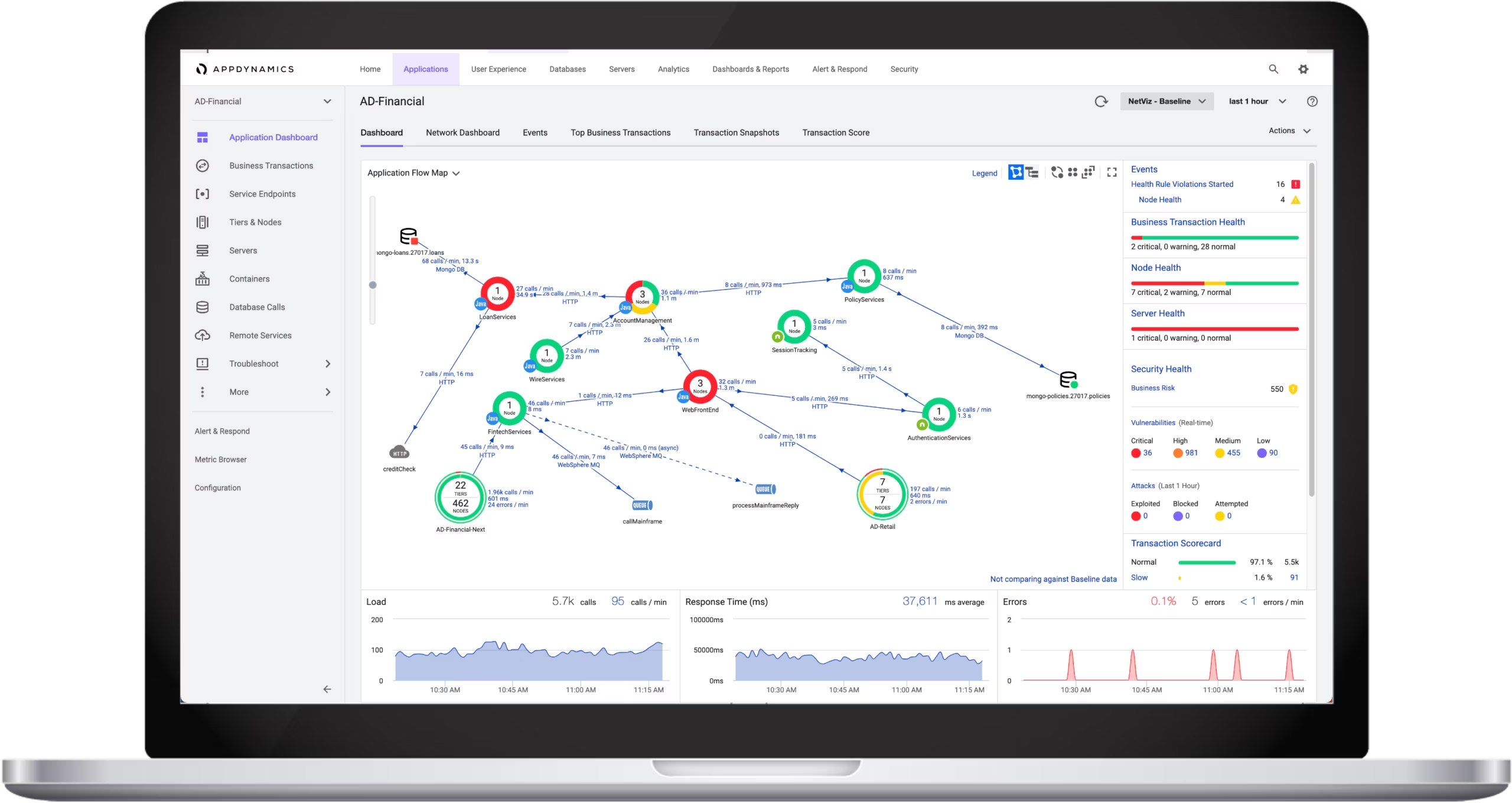
3. AppDynamics
AppDynamics is an application performance monitoring solution that provides end-to-end visibility into application behavior across on-premises and cloud environments. It focuses on linking technical performance metrics with business outcomes, allowing teams to detect issues early and understand their impact.
Key features:
- Performance monitoring: Tracks application performance continuously to detect issues before they affect users
- End-to-end visibility: Provides visibility across the full application stack in multicloud environments
- Root cause analysis: Uses analytics and machine learning to identify and diagnose performance issues
- Business correlation: Connects application performance data with business metrics and outcomes
- Secure monitoring: Includes role-based access control and secure architecture for application oversight
Source: Cisco
Network and Infrastructure Mapping Tools
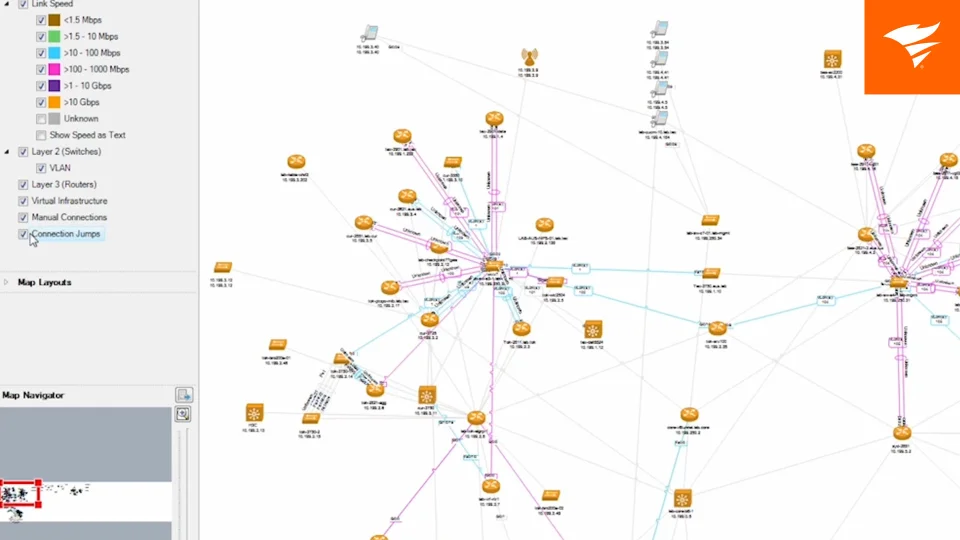
4. SolarWinds Network Topology Mapper
SolarWinds Network Topology Mapper is a network mapping tool that automatically discovers devices and builds topology diagrams. It uses multiple discovery protocols to identify network components and maintain updated maps as the environment changes.
Key features:
- Automated network discovery: Identifies devices using protocols such as SNMP, ICMP, and WMI
- Dynamic topology mapping: Creates and updates network maps as infrastructure changes
- Multi-level mapping: Supports detailed logical diagrams of complex network structures
- Automated diagram creation: Generates network diagrams without manual effort
- Topology change detection: Detects and reflects changes in the network layout automatically
Source: SolarWinds
5. ManageEngine OpManager
ManageEngine OpManager is a network monitoring and mapping tool that provides visibility into network devices, servers, and virtual environments. It combines monitoring, visualization, and troubleshooting features to help identify and resolve issues quickly.
Key features:
- Real-time network monitoring: Tracks performance, availability, and health of IP-based devices
- Comprehensive visualization: Offers topology maps, business views, and data center layouts
- Root cause analysis: Enables drill-down analysis to identify the source of issues
- Distributed monitoring: Supports monitoring across multiple locations from a central console
- Integrated alerting: Provides alerts and notifications based on fault detection and thresholds
Source: ManageEngine
6. NetBrain
NetBrain is a network automation and mapping platform that focuses on real-time visibility and automated troubleshooting. It creates dynamic maps and uses automation to analyze network behavior and prevent outages.
Key features:
- Automated network discovery: Generates maps and documentation of hybrid network environments
- Dynamic mapping: Creates real-time topology and path visualizations
- AI-driven automation: Uses automation to analyze changes and prevent configuration drift
- Continuous assessment: Monitors networks to identify risks and ensure compliance
- Integrated troubleshooting: Speeds up issue identification and resolution with automated workflows
Source: NetBrain
IT Asset and Configuration Mapping Tools
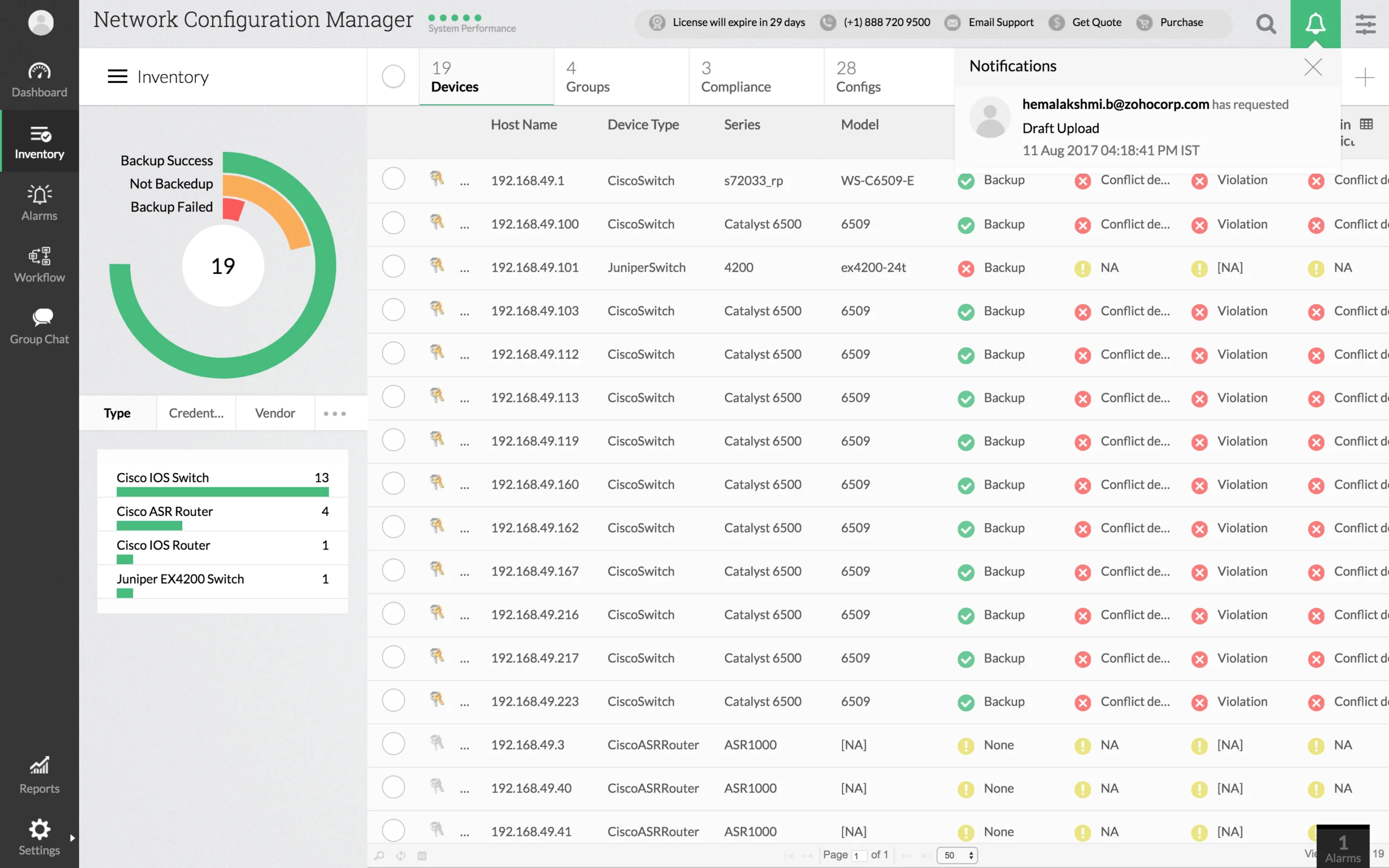
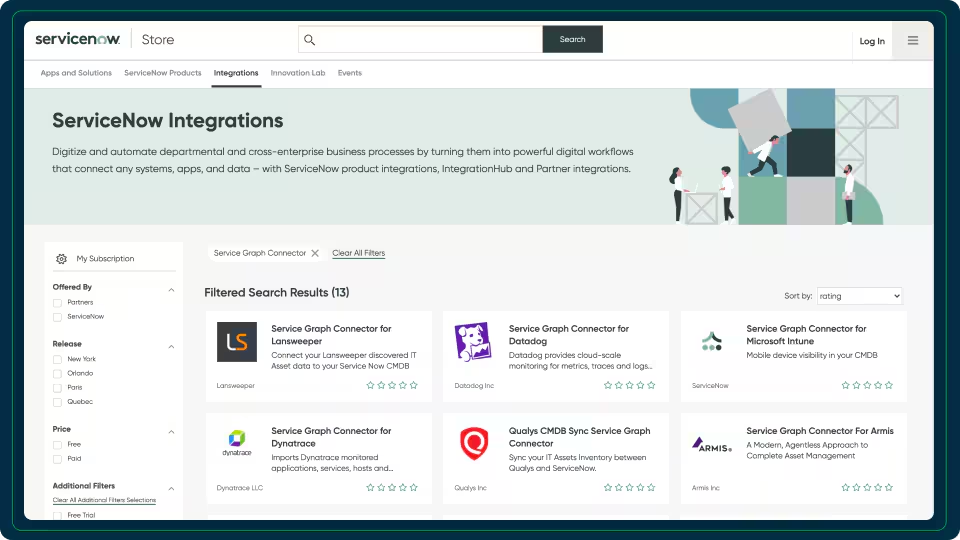
7. ServiceNow CMDB
ServiceNow CMDB is a configuration management database that acts as a centralized system of record for IT assets and their relationships. It integrates data from multiple systems to provide a unified and accurate view of configuration items across the enterprise.
Key features:
- Centralized data repository: Stores and manages configuration item data in a single system
- Data integration: Uses connectors to pull data from multiple IT systems
- Relationship mapping: Visualizes dependencies between assets and services
- Automated data population: Continuously updates data using automated discovery tools
- Visualization and reporting: Provides maps and reports to understand infrastructure context
Source: ServiceNow
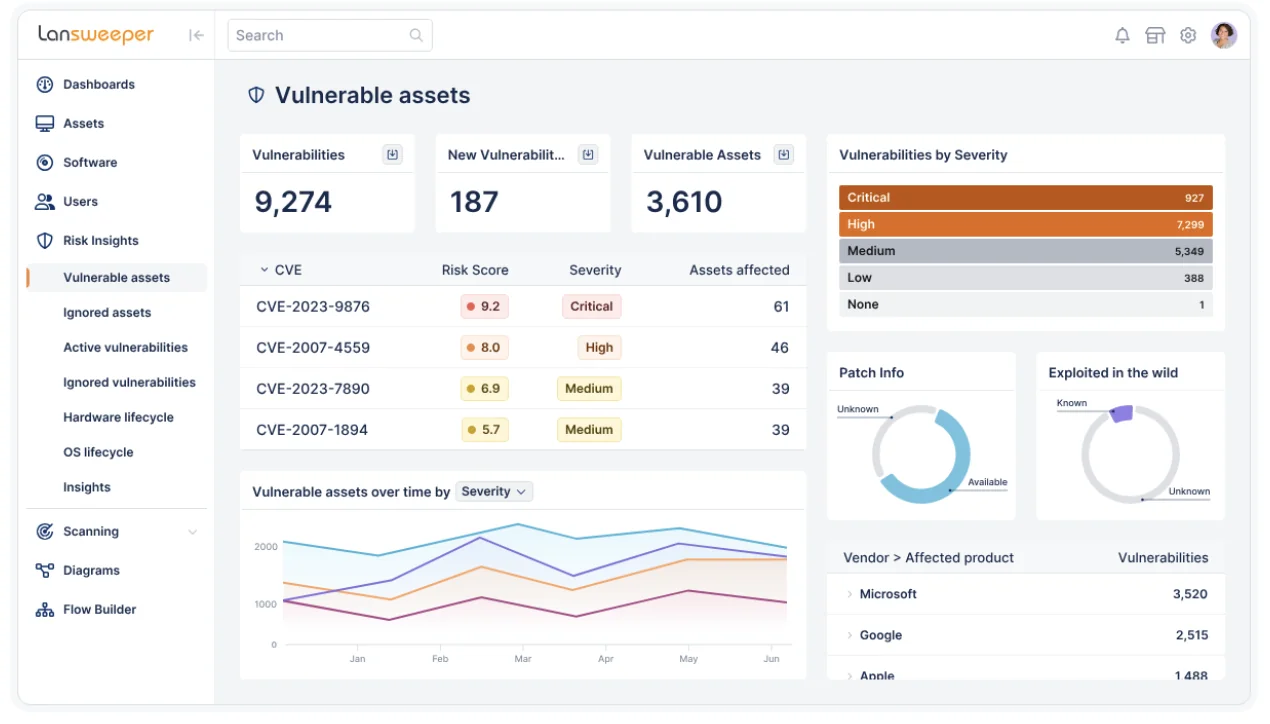
8. Lansweeper
Lansweeper is an asset discovery and inventory platform that provides a unified view of IT, OT, cloud, and IoT assets. It focuses on continuously discovering and enriching asset data to support IT and security decisions.
Key features:
- Comprehensive asset discovery: Identifies all assets across environments, including unmanaged devices
- Unified asset inventory: Consolidates asset data into a single, consistent view
- Contextual insights: Enriches assets with risk, lifecycle, and relationship data
- Continuous validation: Keeps asset data accurate and up to date automatically
- Integration capabilities: Shares asset intelligence with ITSM, CMDB, and security tools
Source: Lansweeper
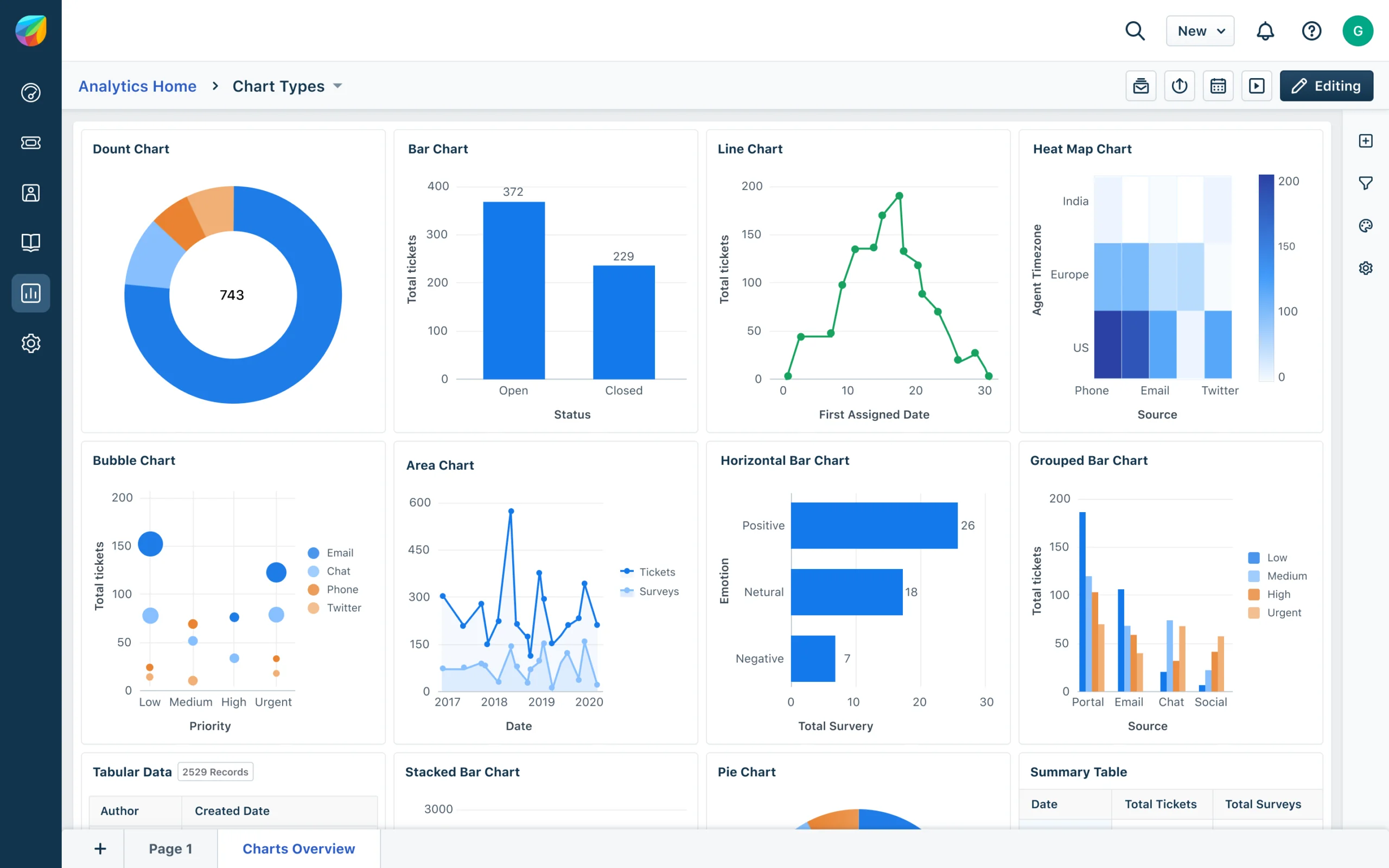
9. Freshworks
Freshworks provides IT service management solutions such as Freshservice, which include asset and configuration tracking as part of broader service operations. It emphasizes ease of use, automation, and AI-driven workflows to manage IT environments.
Key features:
- Integrated ITSM platform: Combines asset management with service management capabilities
- AI-driven automation: Uses AI to simplify service operations and workflows
- Rapid deployment: Designed for quick implementation with minimal complexity
- Unified service operations: Connects asset data with incident and service management processes
- Scalable architecture: Supports growing environments with flexible and modular tools
Source: Freshworks
Defining the Ideal ADM Tool for IT Mapping
The critical nature of IT mapping is a foundational process that enables any organization to operate, change, and grow while being secure, resilient, and profitable. If there are four words that define the needs of any tool for an organization in the digital age, they would likely be comprehensive, fast, agile, and simple. These apply to IT mapping as well.
Comprehensive
When seeking the ideal ADM tool, it must first be comprehensive so that it maps all IT infrastructure, applications, dependencies, and services across all environments in real time. It must be capable of predicting change via integrated analytics to differentiate between various topologies as it audits changes.
Related content: Read our guide to network topology mapping
Comprehensive alerts should bolster this analysis to pinpoint performance and functionality challenges. The same level of reporting will enable proactive corrective action and business planning for everything from cloud migration and data center transformation to BCDR, security, access, and change management.
Related content: Read our guide to vmware networking basics
Speed and Agility
An ideal mapping tool must have a very fast and easily repeatable process, which requires a great deal of automation and visibility via a single dashboard. The resulting transparency and agility enable both pre- and post-migration mapping and automatic discovery of anything with an IP address to plan long-term hybrid multi-cloud strategies. It can also track the constant changes in the app development lifecycle (including containers, microservices, and API endpoints) and virtualized environments.
Simplicity
The simplicity, repeatability, and speed of the ideal ADM tool enable a consistent real-time view of the global environment. It also makes the resulting data easily available to IT and the business to maximize operational efficiency and innovation. It’s imperative that the tool provide visibility across all networks on the application layer in real time.
Related content: Read our guide to network address translation
This delivers critical data for microsegmentation that fosters maximum security and a zero-trust model for user and app access to thwart cyberattacks. Finally, the ideal ADM tool will do all this while integrating with existing third-party tools and never affecting performance so that the organization always operates with the highest efficiency.
How Faddom Helps With IT Mapping
IT mapping is no longer a static documentation exercise but a continuous, real-time requirement for managing modern hybrid environments. As infrastructure becomes more dynamic, traditional approaches like manual mapping, siloed cloud tools, or outdated CMDB data struggle to provide the accuracy and visibility needed for effective decision-making, risk management, and operational efficiency.
A real-time, automated approach to application dependency mapping is essential to maintain control, especially for initiatives like cloud migration, data center transformation, and cybersecurity. Faddom enables organizations to achieve this by delivering continuous, accurate visibility into dependencies across their entire environment, helping teams reduce risk, improve performance, and operate with confidence in an increasingly complex IT landscape.
IT Documentation
Authored by Faddom
- [Guide] IT Documentation: 9 Standards and Best Practices
- [Guide] Network Documentation: What to Document & 4 Best Practices
- [Product] Faddom | Instant Application Dependency Mapping Tool
ITOM
Authored by Faddom
- [Guide] What Is IT Operations Management (ITOM)? Functions, Tools & Tips
- [Guide] ITOM vs. ITSM: Differences, Similarities & Using Them Together
- [Product] Resource and Cost Optimization with Faddom
Data Security
Authored by Cloudian