Whether it is called periodic scanning or active scanning, the fact is that it is an insufficient form of scanning. Today’s complex and fast-paced data centers need continuous scanning capabilities, and this can only be done effectively with passive mapping technology.
Learn more in our detailed guide to agentless scanning vs agent-based scanning
For example, periodic active scanning will usually be scheduled by an IT admin or vendor of choice and done during off hours because it has a heavy impact on network performance. This can be sufficient from a user’s perspective, but it is not enough when it comes to attaining an accurate understanding of a data center. (For more information, see our guide to it asset management.)
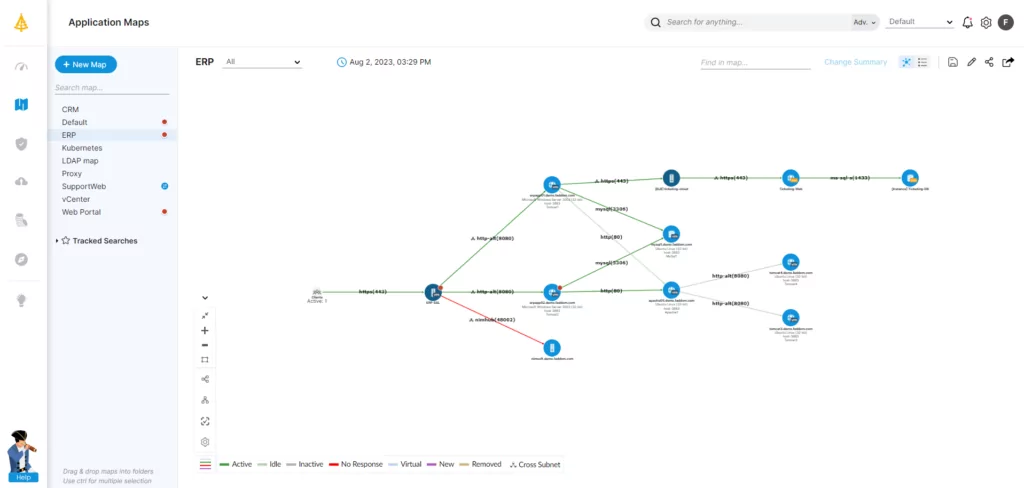
In contrast, continuous passive scanning gleans its intelligence from a complete set of data and provides an accurate map of dependencies and traffic throughout the day – including when you are scaling up performance at peak performance. No additional network traffic is created. Since it does not touch any endpoints, it creates no risk of disrupting critical processes.
Learn more in our detailed guide to enterprise architecture frameworks
Since passive monitoring technologies use no credentials, they are far better choices for creating baselines, scaling to monitor large amounts of data, and ensuring zero impact on performance.
Here is a summary of the further differences between active scanning and passive scanning.
This is part of a series of articles about IT Asset Management
Table of Contents
ToggleSecurity Vulnerabilities
When using active scanning, users need to open firewalls and give server credentials. Sometimes they need Internet connections – through which data can leak out. When using passive scanning, there is no need to open firewalls, provide server credentials, or connect to the Internet. Internal data does not need to leave your environment.
Ease of Deployment
With active scanning, users must give credentials and open firewalls to all servers. This is also difficult and time consuming in big environments. In segmented environments, it might also necessitate multiple deployments. It might not work with multiple active directory instances.
With passive scanning, there is automated deployment and configuration of an environment. Often, they can be fully deployed in under an hour.
Time to Value
Because of the complicated and lengthy deployment issues, users will not see value from active scanning immediately even if they will see it in the medium term.
With passive scanning, users receive immediate value and can see insights quickly once the deployment is complete.
System Resource Use
Active scans can access your servers and can impact them. This can also cause significant network overhead because the entire network is being scanned. Because of this risk, the results and schedules of these scans should be meticulously recorded in your IT documentation.
In contrast, passive scanning does not access servers at all. Passive scans cannot impact them or impact the environment.
Accuracy
Companies using active scanning have blind spots between scans because the information is not constantly updated in real time. Firewalls that are blocking connections can cause scans to miss areas of the network.
Passive scanning can discover all applications and their dependencies in detail in real time. The resulting maps are continuously and automatically updated. There are no blind spots.
Scalability
Active scanning is only somewhat scalable because users have to give credentials and open firewalls. Bottlenecks can arise from one thing having to scan an entire network.
With passive scanning, it is easy to scale from a single server to a large data center. Passive scanners usually use lightweight protocols that can scale to large environments easily.
Pricing
Active scanning tools can cost more than $100,000 per year. Segmented environments can force the purchase of multiple licenses for the same deployment.
Passive scanning tools are far cheaper, and one license is needed to map an entire environment.
If you’re interested in IT mapping software with passive scanning, schedule a call with our expert team!