Openshift Virtualization: Features, Architecture, and Tutorial
What Is Red Hat OpenShift
IT Academy
Guides and Whitepapers
Meet Faddom
Matt Mauchley
Systems Engineer Manager, CHG Healthcare
Pricing
Map your entire on-premises and cloud IT environments as well as business applications without agents in as little as 60 minutes!


































Perimiter Defense is not Enough
Think of microsegmentation as a castle. The moat and the outside walls provide the first line of defense. But in the event they are breached, the rooms inside provide a critical second line that can give the castle defenders time to rally and regroup, slowing and defeating intruders who are attacking.
Microsegmentation, the process of logically dividing the data center and cloud environments into distinct and isolated security segments, adds a layer of defense just like fortified rooms in a castle. It works to limit infiltrations from spreading throughout your entire IT infrastructure by isolating them instead.
Map east-west traffic
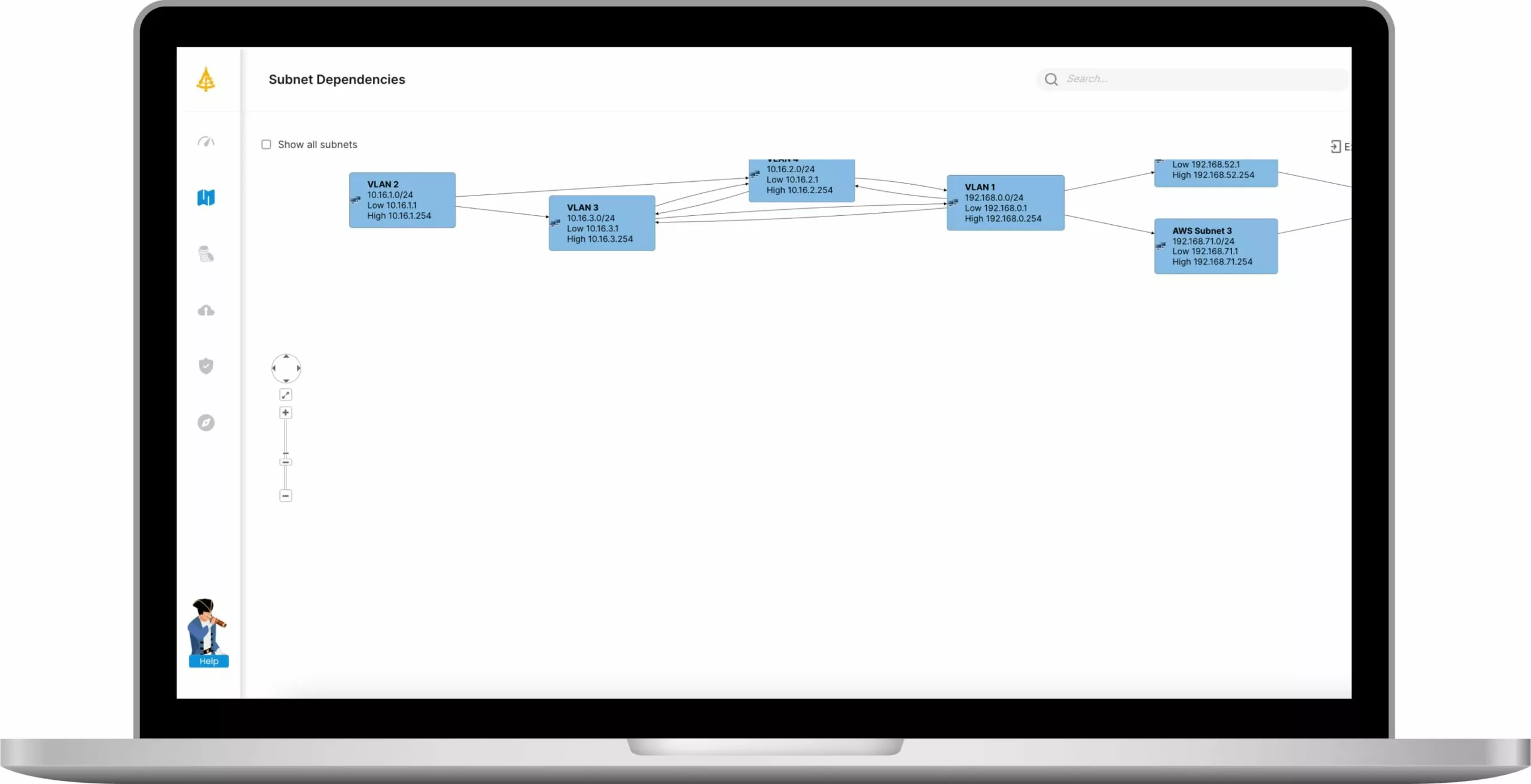
Get dependencies between subnets
Build segment groups with rules
Have Accurate Infrastructure Maps
Map Your Castle to Properly Protect It.
To defend your castle, you must understand where your assets are and how to defend them. Your winning edge is enhanced with visibility into all network traffic both inside your data center and out in the cloud.
But before you can correctly define those zones or “rooms” and set policies around how to control them and who can enter, you need a map of your entire IT environment. This map will allow you to see where clusters are occurring (such as servers) and how to isolate them.
Protect Yourself in THE STORMY SEAS OF IT



Use faddom to gain 24/7 visibility in the rocky seas of it
Be proactive and see your first maps within one hour of deploying Faddom in your environment
Lightweight. No agents. No credentials. No firewall changes needed. Works offline
Whether you are an IT consultant, a small business or a large enterprise, we have a plan for you
Map Your Entire Hybrid IT Environment. No Credit Card Needed
Your organization is your castle. Keep the intruders out. But if they do infiltrate, create a full IT map so you can have a plan to give them the boot.
Map all your on-prem servers and cloud instances, applications, and dependencies
in under 60 minutes.
Get a 14-day FREE trial license.
No credit card required.
