What Is Network Detection and Response?
Network Detection and Response (NDR) is a cybersecurity solution that monitors network traffic to identify malicious activity and respond to threats. It uses machine learning and behavioral analysis to detect suspicious patterns and anomalies that may indicate cyberattacks, even those that bypass other security tools. NDR solutions provide visibility into both east-west (internal network) and north-south (network perimeter) traffic, enabling organizations to detect and respond to threats within their network infrastructure.
NDR tools use techniques like deep packet inspection, flow analysis, and machine learning to spot anomalies that may indicate malicious behavior. They can detect advanced persistent threats, lateral movement, and command-and-control communications that often go unnoticed by signature-based security systems.
Once a potential threat is detected, NDR platforms provide security teams with context, such as the source, destination, and nature of the activity. Many also include automated response features, such as blocking traffic or isolating compromised devices, to contain incidents before they escalate.
Table of Contents
Toggle- What Is Network Detection and Response?
- Why is an NDR Solution Important?
- What Are the Benefits of NDR?
- How Does Network Detection and Response Work?
- Key Features and Capabilities of NDR Solutions
- What Types of Threats Do Network Detection and Response Solutions Uncover?
- Potential Drawbacks and Limitations of NDR
- Choosing a Network Detection and Response Solution
- Harness the Power of ADM with Faddom
This is part of a series of articles about Network Security-FM
Key features and capabilities include:
- Continuous network monitoring: NDR continuously monitors network traffic, including both internal and external communications, to detect malicious activity.
- Behavioral analysis: NDR solutions use machine learning and behavioral analytics to establish a baseline of normal network behavior and identify deviations that indicate malicious activity.
- Anomaly detection: NDR excels at detecting unknown threats and attacks that bypass traditional signature-based security solutions.
- Threat hunting: NDR provides tools and capabilities to investigate suspicious activity and identify the scope and impact of potential threats.
- Automated response: NDR can automate responses to detected threats, such as isolating infected devices or blocking malicious traffic, or integrate with other security tools for a coordinated response.
- Integration: NDR solutions can integrate with other security tools like SIEMs (Security Information and Event Management) and EDRs (Endpoint Detection and Response) to create a comprehensive security posture.
NDR is important for:
- Enhanced threat detection: NDR can detect threats that other security solutions might miss, including sophisticated attacks and insider threats.
- Reduced mean time to detect (MTTD) and mean time to respond (MTTR): By automating detection and response, NDR helps organizations quickly identify and mitigate threats, minimizing potential damage.
- Improved visibility: NDR provides a more comprehensive view of network activity, enabling security teams to better understand their security posture and identify areas of weakness.
- Protection against evolving threats: NDR’s machine learning and behavioral analysis capabilities allow it to adapt to new and evolving threats, providing ongoing protection.
Why is an NDR Solution Important?
NDR is a key component of a security operations center (SOC) because it delivers visibility into network activity that other tools cannot provide. While endpoint detection and response (EDR) tools focus on activity inside individual devices and security information and event management (SIEM) systems analyze log data, NDR monitors all device-to-device interactions across the network. This “aerial view” helps security teams correlate activity between endpoints and logs, enabling faster and more accurate investigations.
Certain threats can bypass both EDR and SIEM. For example, attacks at the BIOS level may evade endpoint monitoring, and malicious activity may never appear in log data. However, once these compromised systems interact with others, their behavior becomes visible to NDR. Likewise, advanced attackers may use encrypted HTTPS tunnels to hide command-and-control sessions or exfiltrate data, but these patterns can be detected through network analysis.
Modern AI-powered NDR platforms collect and store relevant network metadata, enrich it with machine-driven security insights, and use it to identify threats in real time. This approach not only improves detection accuracy but also supports thorough, conclusive incident investigations. By filling the visibility gaps left by other SOC tools, NDR aids in defending against advanced and evasive cyber threats.
What Are the Benefits of NDR?
Network Detection and Response delivers value by providing deeper insight into network activity and enabling faster, more effective threat mitigation. It bridges visibility gaps between other security tools and equips teams with actionable intelligence to stop attacks before they cause damage.
Key benefits include:
- Comprehensive network visibility: Monitors all traffic across the environment, including east-west traffic between internal systems, which often goes unseen by perimeter tools.
- Detection of advanced and stealthy threats: Identifies tactics like lateral movement, beaconing, and encrypted command-and-control channels that evade traditional signature-based systems.
- Faster incident response: Provides enriched alerts with context, allowing security teams to investigate and contain threats quickly.
- Reduced dwell time: Detects malicious activity earlier in the attack chain, limiting the time adversaries spend in the network.
- Improved threat correlation: Integrates with EDR, SIEM, and other SOC tools to connect related events and build a complete attack narrative.
- Support for compliance and forensics: Retains historical network data to meet regulatory requirements and aid in post-incident analysis.
- Automated containment: Can isolate compromised systems or block malicious connections without manual intervention, reducing risk and workload.
How Does Network Detection and Response Work?
NDR works by continuously collecting and analyzing network traffic data from across an organization’s environment. Data sources include network taps, SPAN ports, and cloud traffic mirrors, which capture both packet-level data and flow records. This raw data is processed to extract metadata such as IP addresses, ports, protocols, and session durations.
Detection engines apply analytics and threat intelligence to this metadata. These engines use methods like statistical anomaly detection, behavioral baselining, and signature matching to identify deviations from normal network activity. For example, an unusual spike in outbound data volume or repeated failed login attempts from a new location could trigger an alert.
When a suspicious event is detected, the system correlates it with related activities, building a timeline that shows how the event fits into a broader attack chain. This context helps analysts distinguish between benign anomalies and genuine threats.
Many NDR solutions also integrate with other security tools to automate responses, such as blocking traffic at a firewall, quarantining a device, or triggering an EDR investigation, reducing the time from detection to containment.
Key Features and Capabilities of NDR Solutions
Continuous Network Monitoring
Continuous network monitoring provides real-time visibility into traffic across on-premises, cloud, and hybrid environments. Unlike periodic scans, it ensures that every connection is observed as it occurs, allowing security teams to detect threats at the moment of compromise rather than after damage has been done. This constant observation is critical for detecting short-lived connections, stealthy command-and-control traffic, and lateral movement attempts.
Behavioral Analysis
Behavioral analysis establishes baselines of normal activity by tracking how users, applications, and devices typically communicate. Once the baseline is defined, deviations such as unusual access times, abnormal data transfers, or unexpected protocol use are flagged for investigation. This technique enables detection of previously unknown threats that do not match predefined signatures.
Anomaly Detection
Anomaly detection relies on statistical modeling and machine learning to identify irregularities in network behavior. For example, a sudden increase in outbound traffic from a server that normally has little activity may indicate data exfiltration. By focusing on outliers instead of predefined rules, anomaly detection helps identify emerging attack techniques and zero-day exploits.
Threat Hunting
Threat hunting capabilities within NDR platforms allow analysts to proactively search for indicators of compromise across historical and real-time network data. Analysts can query traffic patterns, pivot between related events, and map suspicious behavior against known attacker techniques. This proactive approach reduces attacker dwell time and strengthens overall incident response readiness.
Automated Response
Automated response features enable NDR tools to take immediate containment actions without waiting for manual intervention. Examples include cutting off malicious sessions, blocking suspicious IP addresses, or isolating compromised devices from the network. Automation reduces the mean time to respond and prevents threats from spreading while human analysts validate and investigate the incident.
Integration
NDR solutions integrate with other security platforms such as SIEM, EDR, and SOAR systems. This allows correlated detection across endpoints, logs, and network traffic, providing analysts with a complete picture of an attack. Integration also enables coordinated responses, such as triggering endpoint isolation from NDR detections or enriching SIEM alerts with network context for faster triage.
What Types of Threats Do Network Detection and Response Solutions Uncover?
NDR solutions are designed to detect a range of threats that often evade perimeter and endpoint defenses. Common examples include:
- Advanced persistent threats (APTs): Long-term, targeted attacks where adversaries maintain stealthy access to a network to steal data or disrupt operations. NDR can spot the subtle lateral movement and unusual communication patterns these attackers use.
- Command-and-control (C2) communications: Connections between compromised systems and attacker-controlled servers, often hidden in encrypted tunnels or disguised as legitimate traffic. NDR detects anomalies in traffic flow, timing, and destination that suggest C2 activity.
- Data exfiltration: Unauthorized transfer of sensitive data outside the network. This can involve large-volume transfers, unusual protocols, or activity at odd hours. NDR identifies these patterns and flags them for investigation.
- Malware propagation: Spread of malicious software within a network, including ransomware and worms. By monitoring device-to-device communications, NDR can detect infection chains even if the malware is previously unknown.
- Insider threats: Malicious or negligent actions by employees or contractors, such as unauthorized access to critical systems or data. NDR can detect unusual behavior from trusted accounts and devices.
- Encrypted threats: Malicious activities hidden in SSL/TLS traffic. While NDR may not decrypt content, it can analyze metadata, handshake anomalies, and traffic patterns to detect suspicious behavior.
Potential Drawbacks and Limitations of NDR
Potential drawbacks and limitations of NDR include:
- High volume of alerts: NDR systems can generate large numbers of alerts, especially in complex or high-traffic environments. Without effective tuning and prioritization, this can lead to alert fatigue and slow incident response.
- False positives: Behavioral and anomaly-based detection can produce false positives when unusual but legitimate activity deviates from established baselines. This requires skilled analysts to investigate and validate findings, which can strain SOC resources.
- Encrypted traffic challenges: While NDR can analyze metadata and patterns in encrypted traffic, it cannot inspect payload content without decryption. This can limit its ability to detect threats that are fully concealed within encrypted sessions.
- Integration complexity: Effective use of NDR often requires integration with other security tools such as EDR, SIEM, and SOAR platforms. Poorly integrated systems can result in fragmented data, slower responses, or duplicated efforts.
- Resource requirements: NDR platforms require significant processing power, storage capacity, and skilled personnel to operate effectively. Organizations with limited budgets or expertise may struggle to maintain optimal performance.
- Evasion techniques: Advanced attackers may use low-and-slow strategies, traffic obfuscation, or legitimate services to blend in with normal activity, making detection harder even for advanced NDR systems.
- Initial learning curve: Because NDR relies on baselining normal network behavior, it can take time to reach optimal detection accuracy, especially in dynamic or frequently changing environments.
Choosing a Network Detection and Response Solution
When choosing an NDR solution, organizations should focus on factors that align with their security goals, infrastructure, and operational capacity. Key considerations include:
- Visibility and data coverage: Ensure the platform can monitor all relevant traffic sources, including on-premises networks, cloud workloads, and remote endpoints. Support for both packet capture and flow-based data provides a more complete picture.
- Detection capabilities: Evaluate the solution’s use of behavioral analytics, machine learning, and threat intelligence. Strong detection should cover known and unknown threats, lateral movement, encrypted traffic anomalies, and emerging attack techniques.
- Integration and automation: Look for seamless integration with existing SOC tools such as SIEM, EDR, SOAR, and firewalls. Automated response capabilities—like blocking connections or quarantining assets—reduce reaction time.
- Scalability and performance: The platform should handle current and projected traffic volumes without latency or data loss. Cloud-native or hybrid architectures can offer flexibility for scaling with business growth.
- Alert quality and tuning: Assess whether the system can minimize false positives through configurable baselines, dynamic thresholds, and context enrichment. High-quality alerts reduce analyst workload.
- Data retention and forensics: Long-term storage of network metadata supports compliance requirements and post-incident investigations. Check retention limits, indexing capabilities, and search performance.
- Usability and analyst support: A clear, well-designed interface with advanced search, visualization, and investigation tools helps analysts quickly interpret and act on findings.
- Vendor support and threat intelligence: Evaluate the provider’s update frequency, quality of threat intelligence feeds, and responsiveness of support teams. A strong vendor relationship ensures ongoing effectiveness.
Harness the Power of ADM with Faddom
Today’s security experts must grapple with how to choose, apply, and integrate from a long list of security tools with an alphabet soup of acronyms. EDR protects endpoints, and its evolutionary successor XDR integrates network, application, and cloud data sources.
The much more comprehensive AI/ML and behavioral analytics of NDR focus on packet data traffic, bringing single-platform, real-time threat detection capabilities, rapid incident response, and comprehensive network traffic analysis to network security in hybrid-cloud scenarios. SOAR solutions can further enable the use of comprehensive analytics and end-to-end automation and integrations. Larger enterprises can maximize their security posture with a combination of EDR, XDR, SIEM, and SOAR systems—with NDR serving as the holistic connection point for more rapid threat detection and response.
Regardless of organizational size and network complexity; visibility, real-time proactive detection, and rapid response are foundational to a constantly changing and complex threat landscape. Network detection and response is revolutionizing the way organizations approach cybersecurity integration with other threat detection solutions and approaches.
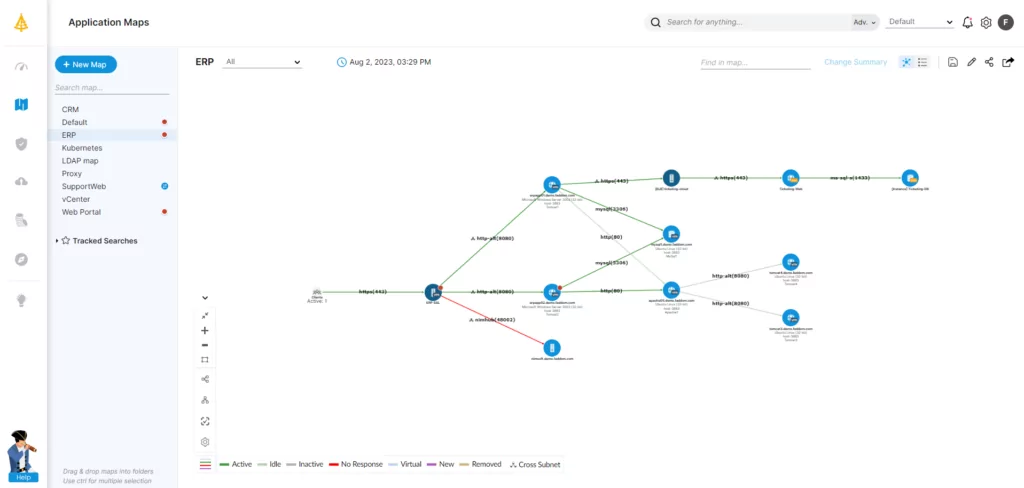
Faddom’s fast and agentless IT infrastructure, network, and application mapping software delivers a complete view of the entire on-premises and cloud IT environment in an hour or less. Users can assess costs, uncover hybrid ecosystems, model workload migrations, and more—without the need for credentials, firewalls, or agents. Its easy deployment, high scalability, and seamless integration with e-tools and products increases the effectiveness of today’s NDR solutions.
Boost visibility into your distributed networks and hybrid cloud environments with Faddom. Start a free trial now!




