What Are AI Security Tools?
AI security tools are software solutions that use artificial intelligence and machine learning to detect, prevent, and mitigate cyber threats. These tools analyze vast amounts of security data, identify patterns, and automate responses to incidents.
By continually learning from new data, AI security tools adapt to evolving attack tactics more quickly than traditional, rule-based systems. Their capabilities cover threat detection, vulnerability assessment, anomaly recognition, automated decision-making, and real-time response actions, enabling more efficient management of complex security environments.
AI security tools are augmentations for established cybersecurity practices, not replacements. These tools work best when integrated into broader security operations, providing insights that help human analysts focus on genuinely critical threats. Their ability to scale across networks and rapidly process data makes them suited for the dynamic threat landscape.
Editor’s note: Added recent information about the AI security market and updated information for AI security tools to reflect features and capabilities in 2026.
Table of Contents
Toggle- What Are AI Security Tools?
- AI Security Tools Market and Trends
- What Types of Organizations Use AI Security Tools?
- Key Types of AI Cybersecurity Tools
- AI Monitoring, Tracking, and Anomaly Detection
- Threat Detection and Response
- AI-Driven Cloud-Native Security
- Full-Lifecycle AI Security Platforms
- How to Choose the Best AI Security Tool for Your Needs
- Conclusion
AI Security Tools Market and Trends
According to recent market research, the global AI security tools market is valued at USD 18,980 million, and is expected to grow to USD 37,560 million by 2034, with a compound annual growth rate of 8.9%. Growth is driven by rising cyber threats, regulatory pressure, and increasing use of cloud technologies.
AI security tools include anomaly detection systems, risk and compliance platforms, behavioral analysis tools, and automated incident response solutions. These tools use machine learning, deep learning, and other AI methods to detect and respond to threats in digital environments.
Market Drivers
The main driver is the increasing complexity of cyberattacks. Organizations face threats such as zero-day exploits, AI-powered malware, and deepfake-based social engineering. AI tools can adapt in real time, which makes them suitable for detecting evolving attack patterns.
Regulatory requirements also push adoption. Laws such as GDPR and CCPA require stronger data protection and monitoring. AI tools help automate compliance checks, detect unauthorized access, and generate detailed audit trails. Around 78% of enterprises now prioritize AI-based security for real-time detection and response.
The expansion of cloud services and IoT further increases demand. Distributed environments require scalable security tools that can process large volumes of data across multiple systems.
Market Challenges and Restraints
High implementation costs remain a barrier. Organizations must invest in infrastructure and skilled professionals to deploy and maintain AI systems. Integration with legacy systems can also create compatibility issues.
False positives are another challenge. AI systems may generate alerts that require manual validation. In addition, limited transparency in some AI models creates trust concerns among security teams.
Data privacy regulations can restrict access to the large datasets needed to train AI models. Strict governance rules may limit how security vendors collect and use data, which can affect model accuracy and improvement.
What Types of Organizations Use AI Security Tools?
Here is a break down of the types of organizations which derive value from AI-based security:
- By type: Anomaly detection tools are becoming central to modern security architectures. They identify zero-day threats by learning normal behavior patterns and detecting deviations. They are widely used in cloud environments and often integrate with SIEM systems to improve detection accuracy and reduce false positives.
- By application: The BFSI sector shows the highest adoption rates. Financial institutions require real-time fraud detection and must comply with strict regulations. Behavioral analytics is used to detect insider threats and advanced financial cybercrime.
- By end user: Large enterprises are the main adopters. Their complex infrastructures require comprehensive protection. They can integrate AI tools into existing security operations centers and allocate budgets for ongoing model training and optimization.
- By deployment: Cloud-based deployment is growing quickly. It provides scalability for AI models that require high computing power. It also simplifies integration with cloud-native security services and reduces the total cost of ownership compared to on-premise setups.
- By technology: Machine learning dominates current implementations. It is widely used for malware detection and user behavior analytics. It offers a balance between detection accuracy and computational efficiency, making it suitable for real-time security operations.
Key Types of AI Cybersecurity Tools
AI Monitoring and Anomaly Detection
AI monitoring and anomaly detection tools continuously analyze data from systems, networks, and applications to identify behaviors that deviate from established norms. These tools apply machine learning models to baseline historical activity, enabling the detection of subtle changes that may signal insider threats, system misuse, or early-stage attacks.
Unlike static rule-based systems, they can uncover previously unknown threats by identifying unusual patterns across traffic volumes, login times, resource usage, or user actions. These tools are particularly valuable in environments with high data volume or dynamic activity, such as enterprise networks or IoT ecosystems.
Learn more in our detailed guide to AI anomaly detection
Threat Detection and Response
AI-powered threat detection tools monitor endpoints, network traffic, cloud environments, and user behaviors to identify suspicious activity and known indicators of compromise. Using supervised and unsupervised machine learning, these systems establish baselines for “normal” operation, flagging outliers such as unusual logins, lateral movement, or anomalous file access.
Rapid identification of such activities shortens the response window, limiting harm from attacks like ransomware or data exfiltration. Threat response solutions automate many aspects of incident handling, from isolating impacted systems to executing predefined playbooks. They also integrate with broader security information and event management (SIEM) or security orchestration, automation, and response (SOAR) platforms.
Cloud-Native Security
Cloud-native security tools leverage AI to manage risks across complex hybrid and multi-cloud environments. These solutions monitor cloud workloads, configuration drift, access controls, and real-time events, helping security teams identify misconfigurations, detect intrusions, and minimize attack surfaces. AI-driven analysis allows these tools to quickly correlate unusual patterns or privilege escalations across dynamic cloud assets.
In addition to threat detection, these tools automate compliance checks and policy enforcement, ensuring adherence to evolving frameworks like CIS, SOC 2, or GDPR. Their ability to scale with elastic cloud infrastructure makes them essential for modern organizations shifting workloads to public cloud or adopting containerized, serverless architectures.
Full-Lifecycle AI Security Platforms
Full-lifecycle AI security platforms provide end-to-end coverage for the entire security process—from threat prevention through detection, investigation, and resolution. These platforms consolidate data from networks, endpoints, identities, and clouds, providing a unified view that helps security teams identify threats more accurately and efficiently.
Such platforms support compliance, risk management, and security operations in complex enterprise environments. Integration with existing workflows lets organizations orchestrate responses, automate remediation, and enforce security policies throughout the IT ecosystem. Full-lifecycle solutions also maintain historical context for incidents, useful for forensic analysis.
AI Monitoring, Tracking, and Anomaly Detection
1. Faddom

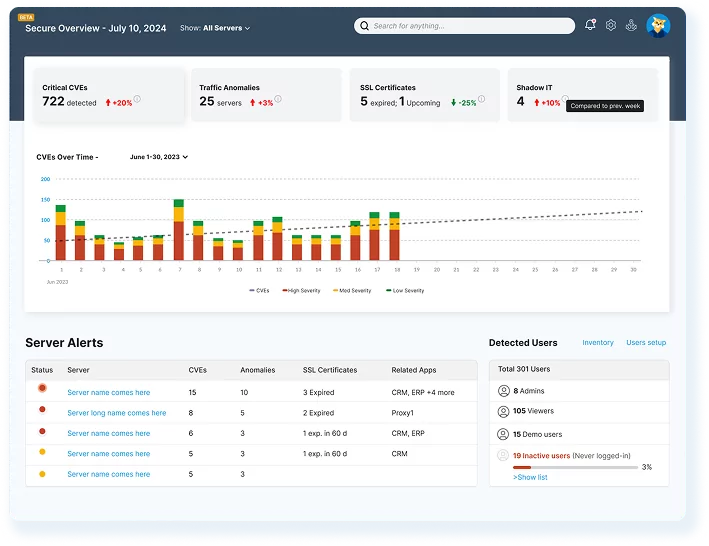
Faddom is an agentless application dependency mapping and AI-powered anomaly detection platform that provides IT and security teams with comprehensive visibility into their environments. By automatically mapping servers, applications, and dependencies across on-premises, cloud, and hybrid infrastructures, Faddom identifies hidden risks that traditional tools often overlook. Its AI-driven insights facilitate the detection of abnormal traffic behaviors, help prevent lateral movement, and enhance segmentation strategies before attackers can exploit vulnerabilities.
Key features include:
- Agentless and Fast Deployment: Get started quickly. Setup can be completed in under 60 minutes, and there is no need for agents or complex configurations.
- Continuous Real-Time Visibility: Enjoy automatically updated maps of applications, servers, and traffic flows.
- AI Anomaly Detection: Automatically identifies unusual traffic patterns, at-risk servers, and potential ransomware activity without relying on manual thresholds.
- Microsegmentation Support: Provides essential context for building and enforcing zero-trust policies.
- Risk Reduction Detects shadow IT, unauthorized access, and risky east-west traffic to eliminate blind spots.
2. Microsoft Azure Anomaly Detector

Microsoft Azure Anomaly Detector is a cloud service that detects anomalies in time-series data through API calls. It supports both real-time and batch analysis and is designed for integration into existing applications without requiring advanced machine learning expertise. The service can evaluate single metrics or multiple related variables and identify structural changes in data trends over time.
Key features include:
- Univariate anomaly detection: Detects abnormal values in a single time-series metric by automatically selecting the most suitable model.
- Multivariate anomaly detection: Analyzes multiple variables and their relationships using a graph attention network to identify system-level anomalies.
- Streaming detection: Evaluates incoming data points in real time by comparing each value to previously learned patterns.
- Batch detection: Processes historical datasets to identify anomalies across a defined time range with a consistent model.
- Change point detection: Identifies shifts in trends or patterns, helping detect structural changes in metrics over time.
Source: Microsoft
3. Dynatrace
Dynatrace provides AI-based anomaly detection across complex, multicloud environments. Its deterministic AI engine analyzes system dependencies and contextual data to identify abnormal behavior, determine root causes, and assess business impact. The platform continuously adapts to changes in dynamic environments and supports predictive capabilities to anticipate future issues.
Key features include:
- AI-driven root cause analysis: Identifies anomalies and traces them to their underlying cause using dependency mapping and causal analysis.
- Alert grouping with AI: Correlates related anomalies into single alerts to reduce noise and minimize alert fatigue.
- Multidimensional baselining: Continuously adjusts thresholds based on live system data, including time-based and seasonal patterns.
- Dynamic environment awareness: Adapts to changing conditions in containerized and cloud-native systems where baselines frequently shift.
- Predictive analytics: Learns traffic and load patterns to forecast future behavior and potential performance issues.
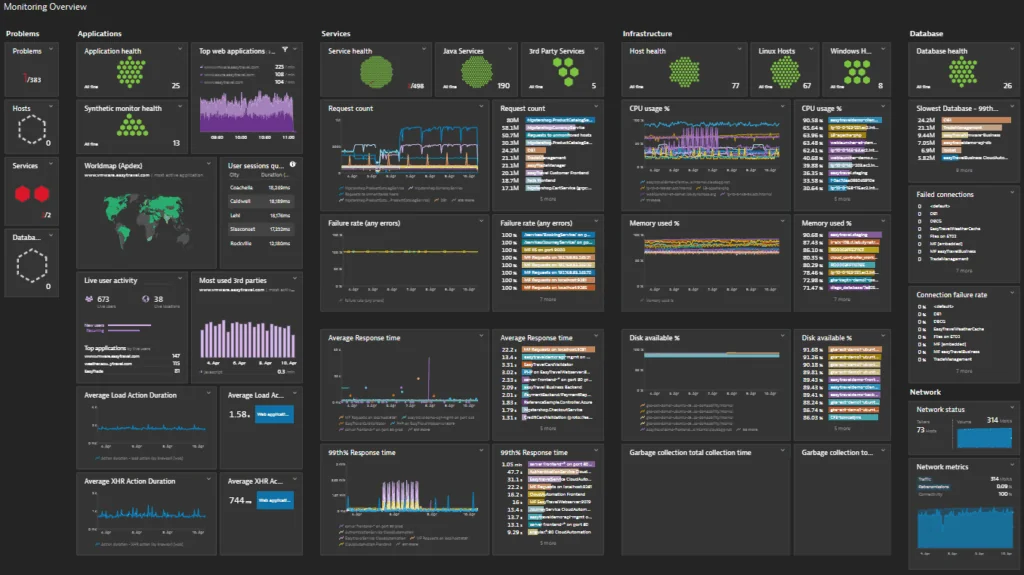
Source: Dynatrace
Threat Detection and Response
4. SentinelOne Singularity

SentinelOne Singularity is an AI-powered security platform that delivers protection, detection, and response across endpoints, cloud workloads, and identities. It uses autonomous and behavioral AI models to prevent malware, ransomware, and zero-day attacks in real time. The platform unifies multiple security functions into a single system to improve visibility and reduce response times.
Key features include:
- Unified endpoint and cloud protection: Uses a single agent to secure endpoints, servers, and cloud workloads across environments.
- Autonomous threat prevention: Applies on-device AI models to prevent malware and reduce attack surface without relying on constant connectivity.
- Behavioral AI detection: Detects zero-day threats and ransomware using static and behavioral analysis across operating systems and cloud platforms.
- Natural language threat hunting: Enables analysts to run investigations and generate summaries using natural language queries through Purple AI.
- Automated incident response: Supports policy-based automation and one-click remediation to contain and resolve threats.
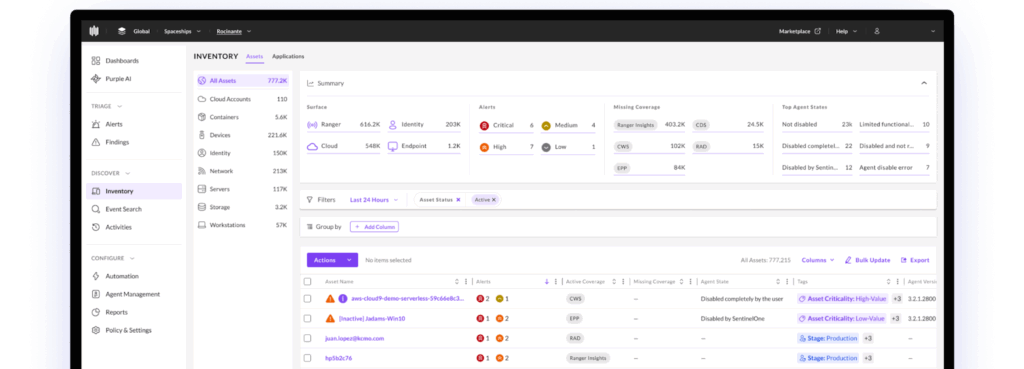
Source: SentinelOne
5. Vectra AI

Vectra AI is a network detection and response platform that uses AI-driven behavioral analytics to detect attacker activity across network, identity, cloud, and SaaS environments. It focuses on identifying real attacker behaviors rather than relying only on signatures. The platform correlates activity across domains to expose lateral movement, privilege escalation, and account compromise.
Key features include:
- Cross-domain threat detection: Detects attacker behaviors across data centers, remote work environments, cloud platforms, SaaS applications, IoT/OT systems, and identity services.
- AI analytics engine: Ingests and analyzes network data to surface behaviors such as lateral movement and misuse of credentials.
- AI-driven triage and prioritization: Automatically triages, correlates, and prioritizes threats to reduce alert noise.
- Identity threat detection: Identifies abuse of privileged accounts and privilege escalation across human and machine identities.
- Cloud threat detection: Correlates activity across cloud roles, regions, and configurations to detect complex multi-cloud attacks.
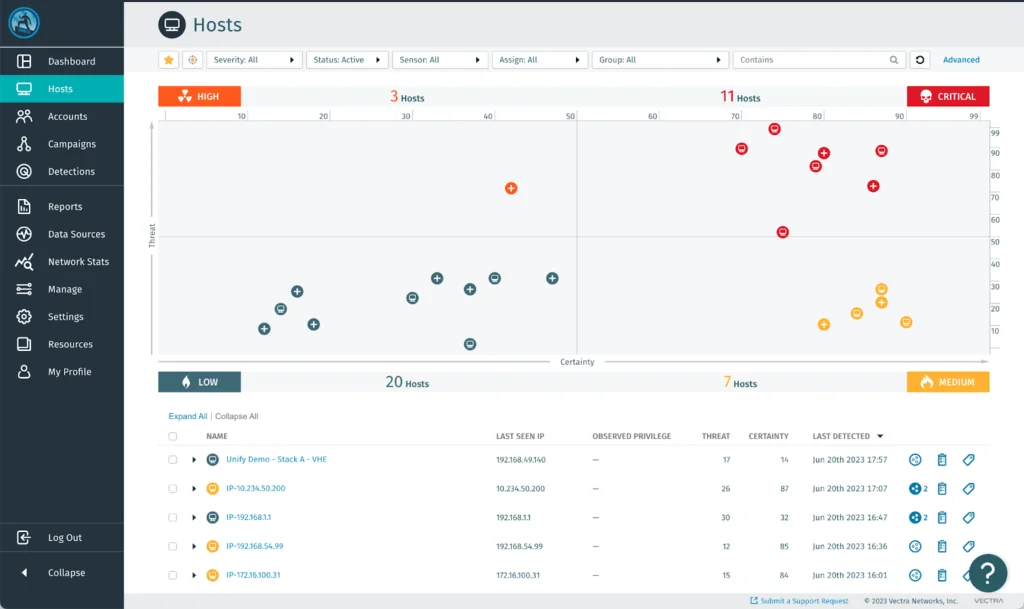
Source: Vectra AI
6. Darktrace
Darktrace / Endpoint is an AI-based endpoint security solution that uses self-learning models to understand normal behavior for each device. Instead of relying on predefined attack signatures, it builds baselines from the organization’s own data to detect deviations. The platform provides real-time detection and autonomous response to contain both known and novel threats.
Key features include:
- Behavior-based threat detection: Learns normal behavior for each endpoint and identifies high-risk deviations.
- Autonomous targeted response: Takes context-aware actions to contain threats without broadly isolating systems.
- Integration with existing EDR: Extends visibility and response by integrating with tools such as Microsoft Defender for Endpoint.
- Automated investigation: Uses AI to triage and investigate incidents, reducing manual analysis effort.
- Coverage for remote and hybrid environments: Maintains protection for devices across on-premises, remote, and hybrid setups.
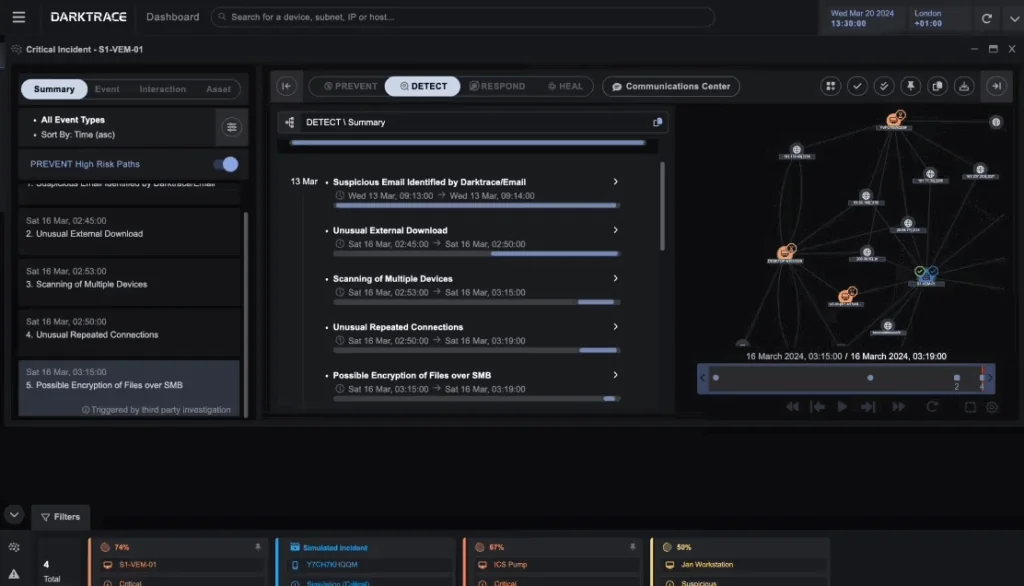
Source: Darktrace
AI-Driven Cloud-Native Security
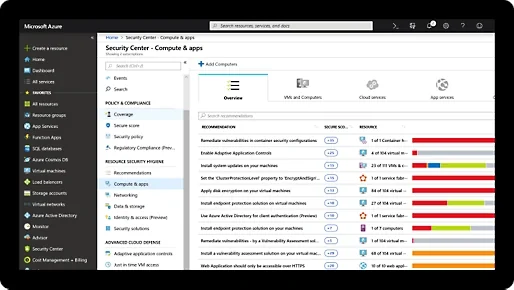
7. Microsoft Defender for Cloud

Microsoft Defender for Cloud is a cloud-native application protection platform that combines posture management, development security, and workload protection. It provides visibility across multicloud and hybrid environments and integrates security controls throughout the application lifecycle. The platform unifies security data to support posture assessment, threat detection, and DevOps integration.
Key features include:
- Unified CNAPP capabilities: Combines cloud security posture management, DevSecOps integration, and cloud workload protection in one platform.
- Cloud security posture management (CSPM): Assesses configurations, applies policies, and tracks secure score across multicloud environments.
- DevSecOps integration: Identifies infrastructure-as-code misconfigurations and exposed secrets in code repositories and pipelines.
- Cloud workload protection (CWPP): Protects virtual machines, containers, storage, databases, and serverless workloads.
- AI security and threat protection: Provides posture management and threat detection for generative AI workloads across their lifecycle.
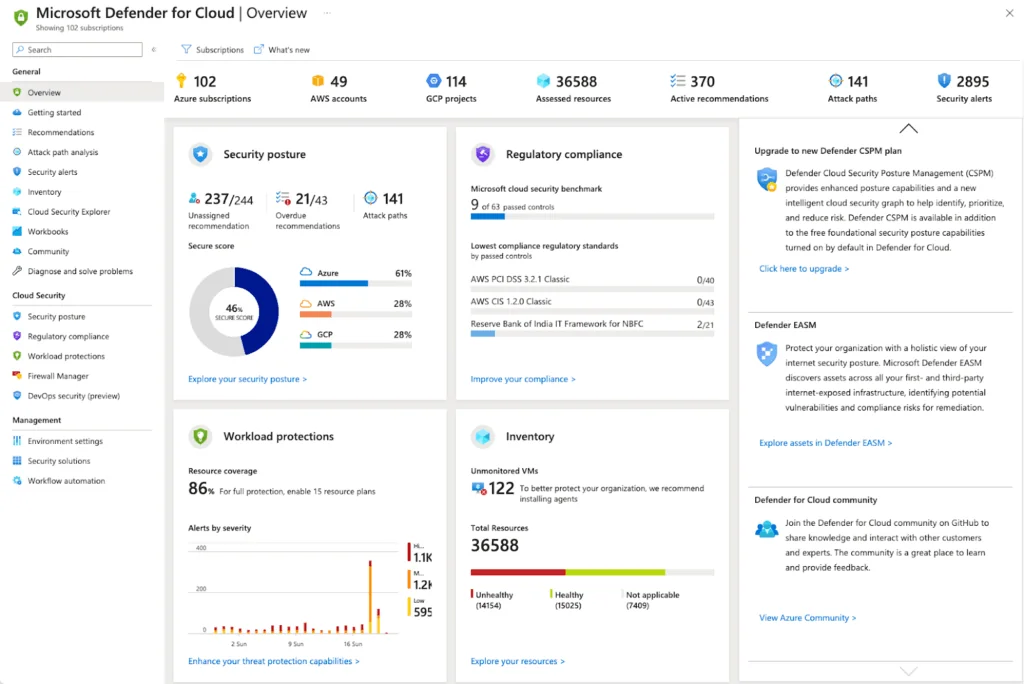
Source: Microsoft
8. Prisma Cloud
Prisma Cloud by Palo Alto Networks is a cloud-native application protection platform that secures applications from development through runtime. It provides visibility and control across code, infrastructure, and running workloads. The platform uses AI-driven analysis to prioritize risks and detect active threats across multicloud environments.
Key features include:
- Cloud security posture management (CSPM): Continuously evaluates cloud resources to detect misconfigurations and enforce security policies.
- Infrastructure and entitlement management: Monitors cloud infrastructure and permissions to reduce excessive access and harden environments.
- Runtime threat detection: Protects hosts, containers, serverless functions, and APIs with in-line protection and defense-in-depth controls.
- AI-powered risk prioritization: Analyzes the blast radius of vulnerable assets to highlight the most critical and exploitable risks.
- AI security posture management (AI SPM): Secures AI applications by monitoring training data, model integrity, and access to deployed models.
- Prisma Cloud Copilot: Provides a natural language interface to investigate issues and take guided remediation actions.
Source: Palo Alto Networks
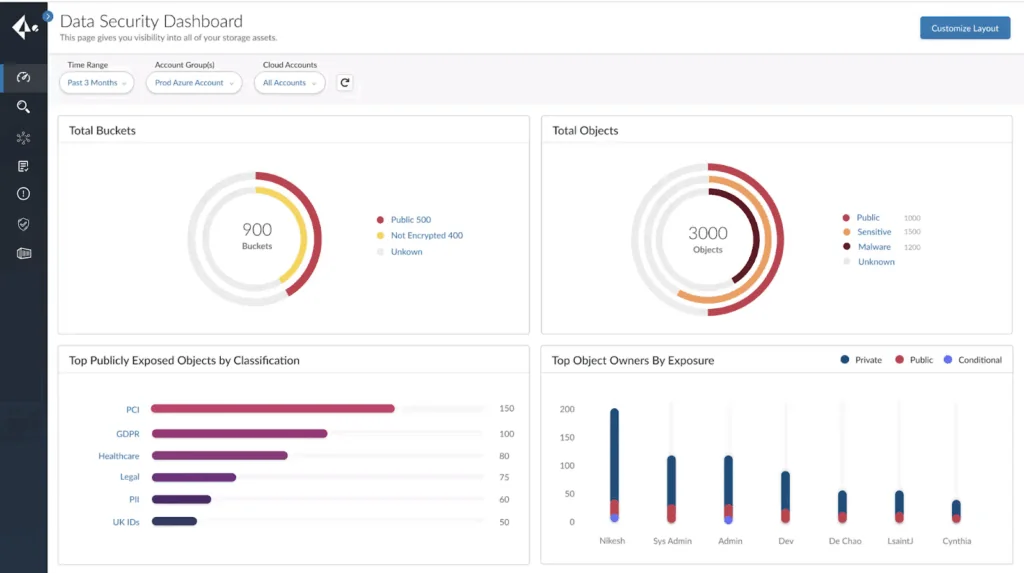
9. Lacework FortiCNAPP

Lacework FortiCNAPP is a unified cloud-native application protection platform that combines posture management, workload protection, identity controls, and detection and response. It connects risk insights with runtime threat data to help teams focus on the most critical exposures and active threats across cloud environments.
Key features include:
- Unified cloud security platform: Integrates CSPM, CWPP, Kubernetes security, CIEM, infrastructure-as-code security, application security, and cloud detection and response.
- Behavior-based threat detection: Uses machine learning to detect unusual behavior, including compromised credentials, ransomware, and cryptojacking.
- Risk prioritization engine: Correlates vulnerabilities, misconfigurations, and threat data to identify likely attack paths and critical risks.
- Cloud identity and entitlement management (CIEM): Provides visibility into users, roles, and permissions to reduce excessive privileges.
- Continuous compliance: Maps assets and configurations to frameworks such as PCI DSS, HIPAA, SOC 2, and ISO 27001.
- Integrated automation and threat intelligence: Enhances detection and response through integration with FortiSOAR and FortiGuard capabilities.
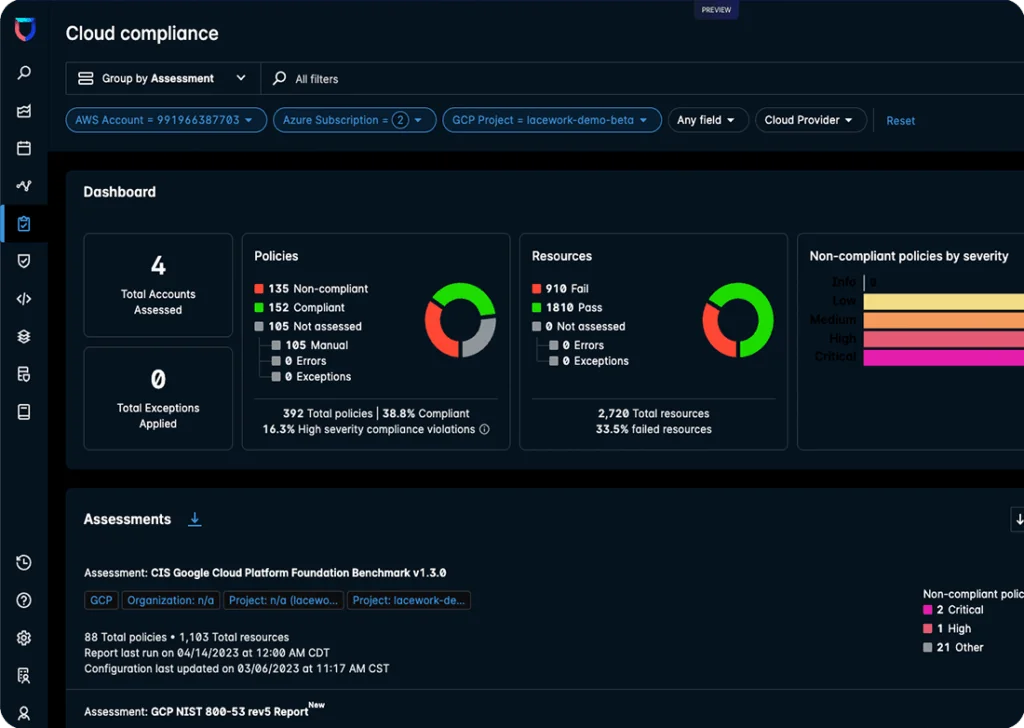
Source: Fortinet
Full-Lifecycle AI Security Platforms
10. Microsoft Security Copilot & Sentinel

Microsoft Security Copilot, integrated with Microsoft Sentinel, provides AI-assisted threat detection, investigation, and response. Copilot uses a chat-based interface to analyze Sentinel incidents, generate hunting queries, and summarize findings. Sentinel supplies security telemetry and incident data, which Copilot uses to deliver contextual insights and guided investigation steps.
Key features include:
- Natural language interaction: Enables analysts to summarize incidents, generate KQL queries, and investigate threats using plain language prompts.
- Unified incident integration: Combines Microsoft Sentinel data with Microsoft Defender XDR incidents for broader context and visibility.
- Plugin-based integration: Supports Microsoft Sentinel plugins, including natural language to KQL query generation.
- Guided investigation and reporting: Produces investigation summaries and executive-ready reports tailored to different audiences.
- Advanced hunting support: Generates and runs KQL queries across supported Sentinel tables to accelerate threat hunting.
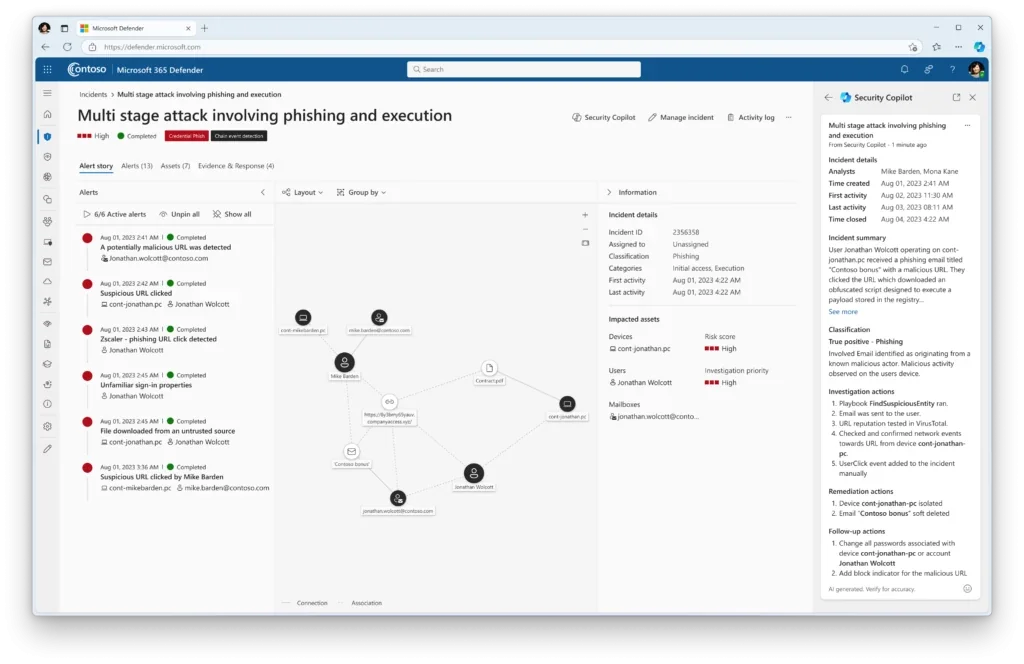
Source: Microsoft
11. Google Security Operations (SecOps)

Google Security Operations is a cloud-native security analytics and operations platform built on Google infrastructure. It unifies threat detection, investigation, and response while processing large volumes of security telemetry. The platform integrates threat intelligence and AI capabilities to reduce manual work and improve investigation speed.
Key features include:
- Scalable security analytics: Stores and analyzes large volumes of telemetry with elastic scalability and continuous threat detection.
- Threat detection: Uses a rules engine, continuous indicator-of-compromise matching, and retrospective analysis.
- Natural language investigation with Gemini: Enables analysts to search logs and create detections using AI-powered conversational queries.
- Integrated SOAR capabilities: Automates response workflows across security tools and environments.
- Security telemetry pipeline: Filters, normalizes, and routes log data to improve detection accuracy and operational efficiency.
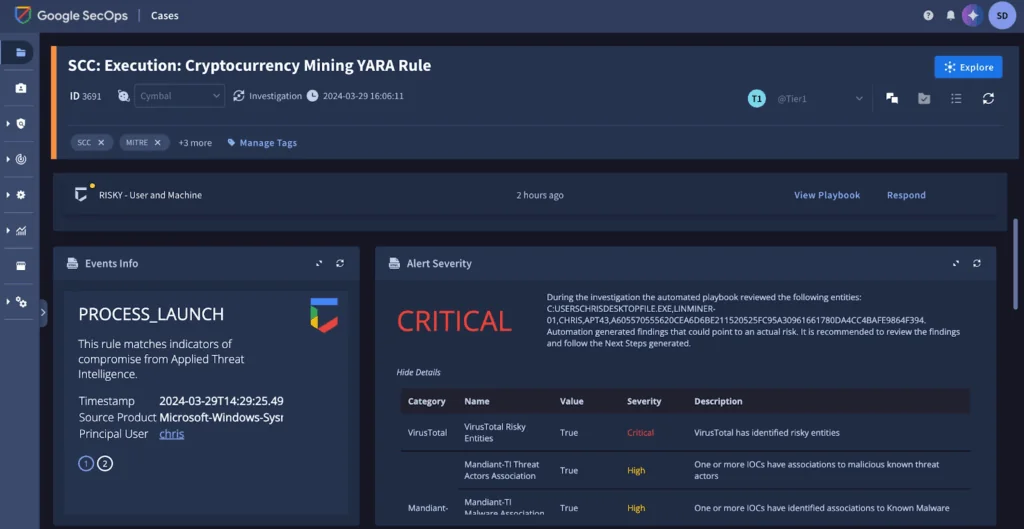
Source: Google
12. Orca Security
Orca Security provides a cloud security platform with a GenAI-powered assistant, Orca AI, that helps teams investigate and remediate cloud risks. It analyzes telemetry across cloud assets and presents findings through a conversational interface. Orca AI assists with risk prioritization, remediation guidance, and anomaly detection across cloud environments.
Key features include:
- Natural language cloud queries: Allows users to ask questions about assets, vulnerabilities, and exposures without complex query syntax.
- AI-generated remediation guidance: Produces actionable remediation steps that can be applied directly in consoles or infrastructure-as-code tools.
- IAM policy optimization: Recommends least-privilege adjustments by comparing assigned permissions with actual usage.
- Alert and asset summarization: Summarizes risk severity, exploitability, attack paths, and exposure context for faster investigation.
- Behavioral anomaly detection: Analyzes workloads and configurations to detect suspicious activity while reducing false positives.
Source: Opus Security
How to Choose the Best AI Security Tool for Your Needs
Selecting the right AI security tool requires aligning its capabilities with your organization’s security maturity, risk profile, and operational constraints. With a growing number of tools offering overlapping features, the key is to prioritize based on specific use cases, integration needs, and the complexity of your digital environment.
Key considerations include:
- Security objectives and use case fit: Identify the primary function you need: threat detection, vulnerability management, fraud prevention, or cloud security. Tools optimized for a specific domain often outperform general-purpose platforms in that area.
- Integration with existing stack: Evaluate how well the tool integrates with your current SIEM, SOAR, EDR, cloud providers, and DevSecOps workflows. Tight integration minimizes disruption and improves data correlation across sources.
- Data coverage and telemetry ingestion: Consider what types of data the tool collects and analyzes—endpoint logs, cloud telemetry, network flows, identity events—and whether it supports your environment at scale.
- AI model transparency and customization: Look for tools that explain their detection logic and allow tuning or model customization. This improves trust, reduces false positives, and aligns with internal threat models or compliance needs.
- Speed and automation of response: Assess how quickly the tool can detect threats and trigger automated responses. Look for features like playbook execution, incident triage, and remediation workflows that reduce time to contain.
- Compliance and reporting support: Ensure the tool can map to relevant regulatory standards (e.g., GDPR, HIPAA, SOC 2) and provides built-in reporting or dashboards for auditors and executives.
- Vendor viability and support: Consider the maturity of the vendor, update frequency, and availability of support. A strong roadmap and responsive support team are essential for long-term reliability.
- Cost and licensing model: Understand pricing structure—whether it’s usage-based, tiered, or flat-rate—and ensure it aligns with your usage volume and growth plans.
Conclusion
AI-driven security tools are becoming essential for managing the scale, speed, and complexity of modern cyber threats. From anomaly detection to full-lifecycle platforms, they provide automation and intelligence that reduce alert fatigue, accelerate investigations, and improve response times. While no tool eliminates the need for skilled analysts, integrating AI into security operations helps teams focus on the most critical risks and stay ahead of evolving attack tactics.