The internet is the world’s fulcrum point of data and communication, which makes the decision between TLS 1.2 and TLS 1.3 a vital consideration for uncompromising encryption security. Some 95 percent of all Google traffic today is encrypted, with many still deciding whether to switch from TLS 1.2 to TLS 1.3 as they weigh the benefits and challenges of both.
What Is TLS?
The evolution of Secure Sockets Layer (SSL) and Transport Layer Security (TLS), which followed SSL, has been long and arduous, as explained in this earlier blog post. As the Internet Engineering Task Force (IETF) has officially deprecated early SSL protocols, the conversation today is more about TLS 1.2 vs. TLS 1.3. The basics are that TLS encrypts communications and data to be transferred via a network and the broader internet.
Table of Contents
ToggleThis makes TLS the safety blanket underneath any engagement in online transactions, confidential information access/sharing, and communication. However, making the case that switching to the latest protocol is likely the best choice requires understanding the differences, challenges, and benefits of TLS 1.2 and 1.3.
Explanation of TLS 1.2
Upon its release in 2008, organizations using TLS 1.2 hailed it as a significant advancement in web security. Its most significant strengths were in its advanced cipher suites, such as the AES-GCM and SHA-256. AES-GCM is a robust symmetric encryption algorithm, while SHA-256 is a reliable hashing algorithm.
TLS 1.2 also introduced an extensible handshake protocol, allowing clients and servers to agree upon the cryptographic algorithms they would use. What users soon found out—and the National Institute of Standards and Technology (NIST) verified—was that TLS 1.2 had some critical weaknesses and vulnerabilities.
Identified Weaknesses and Vulnerabilities in TLS 1.2
Despite the changes to SSL certificates and decryption keys, SSL/TLS vulnerabilities have been an ongoing threat to server security and a catalyst for improvements. One of the first and most prevalent vulnerabilities was the TLS 1.0 cipher block chaining mode, which led to the 2011 BEAST man-in-the-middle attack. This was followed by the Heartbleed vulnerability in the OpenSSL library in 2014 and the Padding Oracle On Downgraded Legacy Encryption (POODLE) attack.
The POODLE vulnerability enabled attackers to steal data by forcing the protocol to fall back to SSL 3.0, which resulted in many organizations quickly patching major servers. Besides being the general blueprint for many points of attack for TLS 1.2, these fallback vulnerabilities and others sped up the development of a more resilient TLS 1.3 standard less than four years later.
Introduction to TLS 1.3
TLS 1.3, which was endorsed and finalized by the IETF in 2018, is far more than just an update of the original protocol. The first significant change is the elimination of several weaker cryptographic algorithms supported in TLS 1.2, resulting in a more streamlined and secure protocol.
One of the most notable improvements of TLS 1.3 is the enhanced handshake process, reducing latency and speeding up connections via fewer round trips. TLS 1.3’s zero round-trip time (0-RTT) resumption provides a quicker and safer way of establishing secure connections, directly combating some vulnerabilities inherent in TLS 1.2.
Addressing Weaknesses and Vulnerabilities of TLS 1.2 in TLS 1.3
The path of TLS 1.2 to TLS 1.3 shows the major improvements in security that build on the lessons learned from past vulnerabilities. However, although TLS 1.3 discards many older encryption algorithms that made TLS 1.2 vulnerable, there are still many users of TLS 1.2. These protocols have seen their own vulnerabilities with the more recently identified Raccoon attack. While these attack vectors and potential vulnerabilities have become far less effective or even possible for hackers, it highlights the differences between the two protocols.
Comparison of TLS 1.2 and TLS 1.3
A standout feature of TLS 1.3 is its insistence on forward secrecy by default. This means that even if a session’s key gets compromised, previous session data remains encrypted and out of attackers’ hands. The resulting performance differences between TLS 1.2 and 1.3 may be clear, but for many organizations, other challenges covered below take center stage.
Performance Differences
TLS 1.3 excels in performance, courtesy of its more efficient handshake process. This makes a noticeable difference in scenarios requiring rapid session establishments, such as loading web pages or initiating secure API calls. TLS 1.3 can thus establish connections faster than TLS 1.2, leading to reduced latency in applications, which is an advantage for web browsing and online streaming.
Compatibility Considerations
While progress is commendable, it doesn’t come without hurdles. Given TLS 1.3’s departure from older ciphers, it can run into compatibility issues with legacy systems or older network devices, as support for older and vulnerable cipher suites has been dropped.
Adoption Rates and Industry Support
Aside from the improvements, the story of TLS 1.2 vs. TLS 1.3 is more about adoption. TLS 1.3 is still in its early stages but is quickly reaching saturation across all major internet industry players. Organizations looking for relevant data on SSL and TLS can refer to the SSL Pulse dashboard from the SSL Labs projects. Out of 135,583 sites surveyed in September 2023, nearly 65 percent of the sites support TLS v1.3, and 99.9 percent support TLS v1.2.
Over 65 percent of AWS service API endpoints support TLS version 1.3 as of September 2023, according to AWS. Other major providers are following suit, with all of them delivering support for TLS 1.2 and most supporting TLS 1.3. They all generally provide some level of backward compatibility, with most deprecating support for earlier versions at different stages.
Microsoft has become the most recent industry player to disable TLS versions 1.0 and 1.1 by default in its OS. This starts with Windows 11 and will move forward with all future Windows releases, but organizations can re-enable them if needed.
The choice between TLS 1.2 vs TLS 1.3 is complicated in the bigger picture since every organization has different considerations for migration feasibility.
Implications for Businesses and Web Users
Organizations must weigh a wide variety of issues when determining how the use of TLS 1.2 or 1.3 will affect their business and users. There are obvious benefits to transitioning to TLS 1.3, such as improved security and performance.
In the age of sophisticated cyberattacks and data access as currency, businesses must find a balance between the highest security measures and easily accessible data and communications protocols. This is true for every sector, from finance and retail to manufacturing, healthcare, and beyond. TLS 1.3 brings enhanced security against data breaches and cyberattacks. But beyond the obvious security advantages, organizations can also benefit from reduced latency, which enhances user experiences on digital platforms.
However, such benefits are not the only consideration when weighing a TLS 1.2 versus a TLS 1.3 transition. According to a recent f5 report prepared by Enterprise Management Associates (EMA), 85% of those surveyed say data security is the biggest benefit of their TLS 1.3 implementation. However, the same report shows that 44% of respondents who made the transition had to roll it back due to loss of traffic visibility.
This is only one of many challenges that give many organizations pause. The better an organization understands its network and IT environment, the easier it is to determine the best TLS version for its needs.
How to Determine Which TLS Version to Use
Despite the many advances in TLS 1.3, its growing adoption rates, and security benchmarks, determining the right TLS version is about more than metrics. Since every organization is different, the decision largely depends on specific business needs and system setups. The three broadest areas for businesses to look at include:
- Compatibility: Foremost, a thorough compatibility check helps avoid system conflicts. Before making the switch, businesses should check for system compatibility with TLS 1.3.
- Resource constraints: Assess if the current infrastructure can handle the new protocol without hitches. Upgrading might require additional resources, both in terms of hardware and software.
- Third-party dependencies: For systems dependent on third-party services, it’s essential to ensure that these services support or are compatible with TLS 1.3.
Although TLS 1.2 continues to play a part in secure internet communications for organizations, evolving cyber threats render it essential for businesses to stay updated. TLS 1.3 offers a more secure and faster online experience, making the transition beneficial for businesses and their users.
Say Hello to Faddom
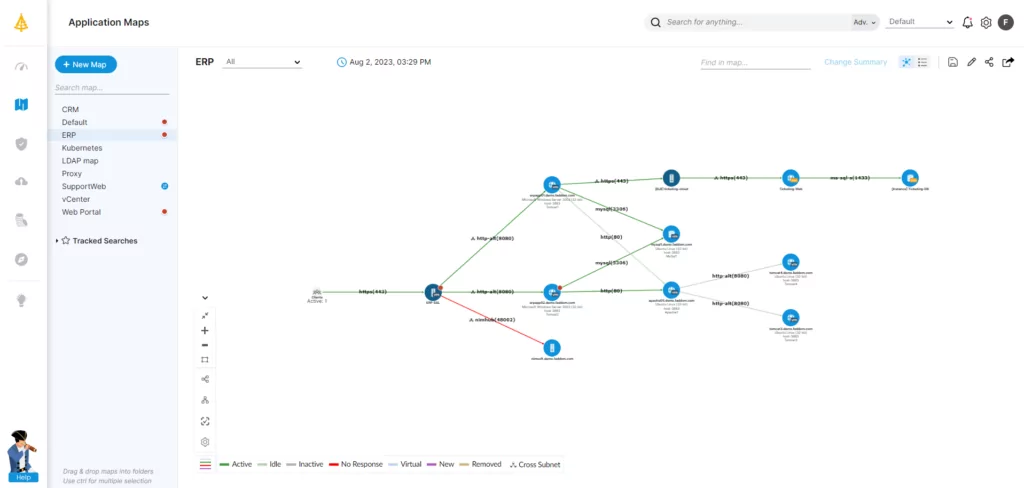
The true success of transitioning from TLS 1.2 to TLS 1.3 comes down to each organization’s comprehensive understanding of its web applications, network, and IT infrastructure. This enables proper planning and timing to maximize benefits and minimize potential pitfalls. To learn how Faddom can map out which versions of TLS you are using, start a free trial today by filling out the form in the sidebar!




