Imagine a world where legacy applications are no longer a burden: Applications scale as the business grows (without breaking the bank), are hardened against the latest cyber threats, and comply easily with all industry regulations while withstanding any audit.
What’s the secret to making all that possible? Legacy application modernization.
This post will explore why many organizations are choosing to modernize legacy applications, along with the benefits and challenges of this transition. It will also describe some of the main obstacles along the way to modernization and how to accomplish it as smoothly as possible, with minimal business disruption.
What Is Legacy Application Modernization?
Legacy application modernization refers to organizations updating and altering existing, often outdated, software systems to better meet modern technology requirements and business goals.
Why would an organization want to do this? The goals of legacy application modernization can vary from one organization to another but are usually motivated by problems that emerge in older applications over the years.
Lackluster Performance and UX
Older applications often get bogged down and don’t perform as well as they could. Plus, their interfaces start to look outdated and often lack the flexibility to modernize user-facing components. Application modernization can enhance performance, usability, and functionality.
One use case for this would be upgrading from a monolithic app to a microservices architecture to achieve massive performance gains.
Integration Constraints
Older applications often don’t integrate well with modern technologies. In an era where APIs reign and interoperability is essential for a wide range of workflows, application modernization can vastly expand the capabilities of a legacy application.
One use case for this would be migrating a standalone on-premises app with limited integrations to a cloud environment that interoperates with an organization’s CRM, ERP, and other business applications.
Limited Capabilities
Older applications may be reaching the end of their practical lifespan and relevance, reflecting the demands of an earlier era and failing to meet today’s needs. Application modernization can extend the lifespan and relevance of existing applications almost indefinitely.
One use case for this would be upgrading an outdated legacy e-commerce platform with AI-driven personalization, mobile optimization, and cloud integration.
Which Modernization Approach Is Best?
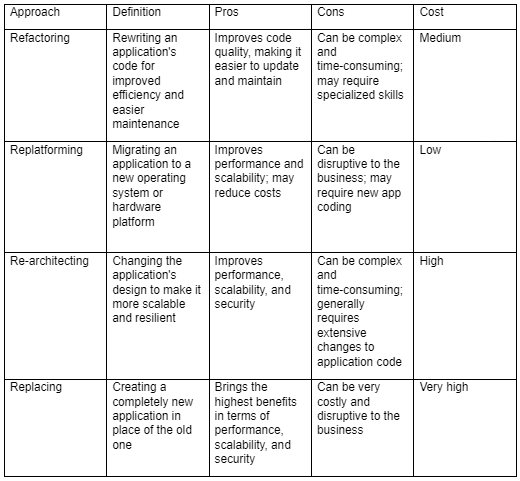
There’s no one right way to proceed with a legacy application modernization project. The four primary approaches have their own pros and cons—as well as different price points:
Regardless of the goals of legacy application modernization, any project of this type requires extensive advance planning—to ensure not only minimal disruption to the business but also the overall success of the project itself.
Why Modernize Legacy Applications?
Organizations of all sizes generally decide to modernize their legacy applications to achieve one or more of the following benefits.
Scalability
As a business grows, it may struggle to handle increasing workloads or higher traffic and data volumes. Modernization can make legacy applications more scalable to meet these demands, as well as more elastic to handle change.
Efficiency
Modernized applications can efficiently scale resources based on demand, enabling better resource utilization and cost-effectiveness.
Market Competitiveness
Competing effectively requires agility to handle varying workloads; scalable applications can adapt more swiftly to market changes.
Security
Modernization means organizations can implement current security features and best practices to build greater resilience for the future.
Vulnerability Management
Legacy applications may be vulnerable to cyberattacks and may lack robust security features like multi-factor authentication (MFA). Modernization strengthens an organization’s defenses against evolving cyber threats, as today’s applications are typically built with security in mind from the start.
Data Protection
Enhanced security measures safeguard sensitive data; this also makes it simpler to achieve compliance with contemporary privacy regulations that didn’t exist at the time that legacy applications were developed.
Incident Response
Modernized systems often have improved incident response capabilities, which reduces the risk of data breaches and system compromises.
Cost
Modernizing legacy applications usually helps cut IT costs, in part through more cost-effective cloud-based solutions. However, there are other areas of cost savings and ROI generation as well.
Operational Costs
Legacy applications can be disproportionately expensive to maintain and upgrade; in some cases, they cannot be serviced at all if staff are no longer with the company.
Return on Investment (ROI)
Increased efficiency and reduced maintenance costs contribute to ROI, but modernization also generates ROI in other ways. These include making an application faster, more interactive, or more intuitive for users, rather than merely a “lift and shift” port of the older application.
Resource Optimization
Modernized applications often require fewer resources; they can also allocate resources more efficiently, leading to direct and immediate cost savings.
Compliance
Modernization can bring an application in line with current industry standards and legal regulations, with the features and controls necessary to adapt to future requirements.
Adherence to Regulations
Legacy systems may struggle to comply with industry and global regulations that have come into play since the applications were released, making compliance (such as around data handling practices) difficult or impossible.
Data Governance
With improved mechanisms for data tracking and auditing, modernized applications make it easier to meet compliance requirements related to safe data management and the protection of sensitive data such as PII.
Risk Mitigation
Modern applications build user trust by adhering to current security and compliance standards; this also cuts the risk of legal issues and fines related to non-compliance.
Challenges in Modernizing Legacy Applications
Modernizing legacy applications is not a simple task. This section discusses some of the biggest speed bumps organizations may encounter.
Architectural Complexity
Legacy applications can be difficult to understand and modify, as the original developers have often left the company. This makes it challenging to find qualified developers who can modify the code—not to mention find replacement parts for older hardware components, if applicable.
Legacy systems also often have complex interdependencies and may be built based on outdated technologies that are no longer supported. Particularly during the transition period, the interoperation of old and new architectures can be difficult to navigate.
Data Migration
Migrating data from legacy applications to new systems can be a complex and time-consuming process. Ensuring data integrity, availability, and security throughout the transition is often overlooked or given a lower priority during the transition. However, without data continuity, many applications cannot perform properly.
Legacy applications may store data in formats incompatible with modern data storage structures, making it difficult to migrate data to new systems without losing or corrupting it. In addition, during the migration process, there’s always a risk of data corruption, alongside downtime and other business disruptions.
This is why proper mapping between old and new data structures is critical, as it will ensure that data remains accessible and usable post-migration.
Vendor Lock-In
Adopting new solutions may be difficult, costly, or disruptive, especially if legacy applications are tied to specific vendors or technologies. While modernizing legacy applications presents a golden opportunity to break free of a vendor who no longer meets the organization’s needs, this must be done with great care.
Organizations may experience compatibility challenges when integrating with non-standard legacy systems. The primary goal here is to ensure that if a change of vendor is required, it has minimal impact on operations.
Skillset Gap
Organizations may not have the skills and expertise in-house to modernize their legacy applications. To ensure success, they may have to hire new staff or even consider outsourcing all or part of the modernization project to a third-party vendor.
It’s essential to assess the organization’s personnel and develop a plan, such as investing in skills upgrading or bringing on new hires, to get a clear picture. This will allow it to address any gaps before starting the modernization process.
Steps for Legacy Application Modernization
By following these steps, organizations can minimize risk and business disruption while also achieving all the benefits of modern applications explored above.
- Evaluate Legacy Systems
Assess the current state of legacy applications and identify areas for improvement. What is the primary motivation for the modernization initiative?
- Define the Problems
Identify the specific problems that need to be addressed by the modernization process. At this stage, it can help to set clear and measurable targets for the modernized app around metrics like speed and engagement. What is the primary target of the modernization? (Be specific.)
- Choose the Right Application Modernization Approach
Select the most appropriate of the four modernization approaches listed above, based on the needs of the organization and the legacy application being modernized. What is the budget? How much time is available for the project?
- Prepare for Future Growth and Changes
Design the modernized application in a way that will be scalable, secure, and compliant. For example, embracing a headless architecture that separates the front and back ends will provide for ongoing improvement of the user experience without major changes to the back end. To prepare for future growth, you will need input from your customers and developers. What’s on their wish lists?
Before Embarking on the Journey…
As noted above, application dependency mapping (ADM) is a vital step that can make the whole process of legacy application modernization so much simpler. ADM lets organizations identify and visualize dependencies between software applications and components. This helps them understand the complex relationships affecting legacy systems and make informed decisions about how to modernize them.
The results of ADM can help streamline legacy application modernization in a few ways.
Understanding Legacy Applications
Identifying all components that make up a legacy application and the interdependencies among components enables organizations to understand how legacy applications function and interact.
Identifying True Business Value
Knowing which applications are most critical to business operations helps to plan and prioritize app modernization, with minimal business disruption along the way.
Pinpointing Bottlenecks and Security Risks
Understanding which legacy apps present the greatest bottlenecks and security risks will help prioritize modernization efforts to improve overall performance and security.
Cutting Costs, Lowering Risks
Lastly, ADM helps identify and mitigate risks such as data loss, downtime, and security vulnerabilities. It also enables organizations to avoid vendor lock-in since it helps them choose a modernization approach that is compatible with their existing systems.
Faddom: A Partner in Modernization
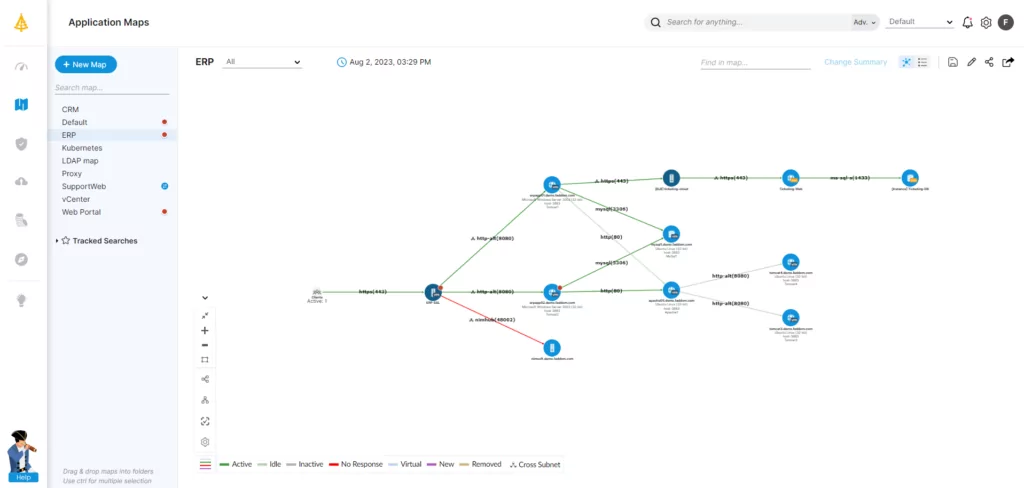
Faddom is a comprehensive ADM tool that maps dependencies for all types of applications, including legacy applications. Designed to help organizations understand all their applications and environments, Faddom makes it easier to plan and execute legacy application modernization projects safely and efficiently via:
- Legacy application topology discovery
- Impact analysis
- Modernization planning and execution
- Reporting and dashboarding for ongoing insights and progress tracking
Faddom documents IT infrastructure both on-premises and in the cloud, producing a comprehensive map of all servers, applications, and dependencies in under 60 minutes. It’s very easy to use and scales seamlessly to make taking the first steps toward application modernization a breeze for organizations of all sizes.
Future-Proofing with Modern, Competitive Apps
Most organizations today have concluded that legacy application modernization is essential to remain competitive and secure. Although there will be inevitable challenges along the way, the benefits, such as scalability, cost savings, and ease of maintenance, are far too great to overlook.
By carefully planning and executing the process, organizations can minimize risk and disruption while paving the way to achieving all the benefits of modern applications. Making application discovery mapping an integral part of that planning process can increase the odds of success while cutting the cost and complexity of any application modernization project.
With Faddom, ADM is fast and easy. To start a free trial and see how quickly Faddom can get to work making your application modernization project easier from start to finish, just fill out the form on this page.




