What Are Network Security Solutions?
Network security solutions include various policies, techniques, and technologies designed to protect the integrity, confidentiality, and availability of computer networks and data. These solutions aim to guard against unauthorized access, misuse, malfunction, modification, destruction, or improper disclosure.
As networks grow, combining on-premises infrastructure with cloud services, these security measures become more crucial in managing complex cybersecurity threats. The evolution of network security has been driven by the increasing sophistication of attacks and regulatory requirements, requiring continuous adaptation and improvement of protection strategies.
Table of Contents
ToggleEditor’s note: Added information about network security market trends and updated details of network security solutions to reflect features and capabilities in 2026.
Today, network security solutions extend beyond basic firewall and antivirus setups. They integrate advanced detection systems, behavioral analytics, and policy enforcement across a myriad of devices. Organizations must encapsulate a multi-layered security strategy to defend against both external intrusions and insider threats.
Network Security Market Trends
According to recent research, the global network security market is valued at USD 27.11 billion and is projected to reach USD 79.29 billion by 2033, growing at a CAGR of 12.7%. This growth is driven by the increasing number of unsecured devices, stricter privacy regulations, and the need for stronger authorization and authentication across enterprise networks.
The solutions segment held the largest share of revenue at 72.6%. This segment includes technologies such as network access control, unified threat defense, data loss prevention, IDS/IPS, firewalls, antivirus, wireless security, DDoS protection, and VPNs. These tools provide real-time threat visibility, identity and access management, and protection across networks, endpoints, and web applications. The services segment, which includes deployment, maintenance, training, and support, is expected to grow steadily due to ongoing licensing and support requirements.
Cloud-based deployment led the market, with organizations adopting subscription-based security models to protect hybrid and multi-cloud environments. Cloud-native tools such as cloud firewalls, encryption, secure web gateways, and identity and access management systems are used to secure multiple entry points in cloud infrastructures. At the same time, on-premises solutions continue to grow as organizations seek greater control and customization.
Large enterprises accounted for the highest revenue share, driven by increased cyberattacks targeting sectors such as IT, banking, healthcare, and government. However, small and medium-sized enterprises are projected to grow at the fastest rate, supported by the expansion of connected ecosystems and cloud-integrated systems.
Types of Network Security Solutions and Technologies
Network Monitoring and Scanning
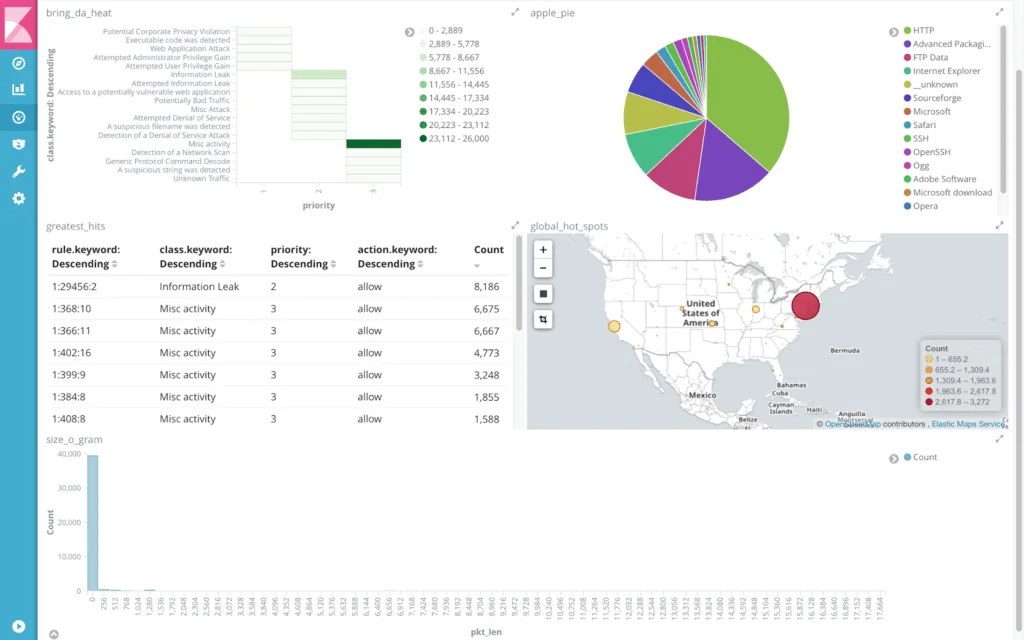
Network monitoring tools continuously observe network traffic, device behavior, and performance metrics to detect anomalies, performance issues, or signs of compromise. These systems collect logs and telemetry from switches, routers, and endpoints to provide real-time visibility, enabling early threat detection and incident response.
Network scanning technologies identify active devices, open ports, running services, and known vulnerabilities. Regular scanning helps assess the attack surface, detect unauthorized assets, and validate compliance with security policies. When integrated with asset management and threat intelligence, scanning tools support proactive risk mitigation.
Next-Generation Firewalls (NGFW)
Next-generation firewalls (NGFW) represent a leap forward from traditional firewall systems. They incorporate in-depth traffic inspection capabilities, application awareness, and integrated intrusion prevention. By doing so, they offer a more nuanced approach to threat detection and control, accommodating the dynamic nature of modern threats.
NGFWs utilize advanced intelligence to decipher encrypted threats and automate responses, reducing the manual effort required for network defense. Integration with threat intelligence feeds provides real-time updates on potential vulnerabilities, ensuring proactive threat management. Organizations benefit from improved visibility into network traffic patterns, allowing for comprehensive monitoring and precise security policy implementation.
Network Access Control (NAC)
Network access control (NAC) is crucial for managing network integrity by regulating device access based on compliance with security policies. NAC solutions assess devices seeking network entry, ensuring they meet defined security criteria before granting access. This vetting process helps prevent unauthorized devices from connecting and potentially compromising network security.
NAC is particularly effective in governing network access in environments with diverse device profiles, such as bring-your-own-device (BYOD) environments. By implementing granular access controls, NAC can enforce network segmentation, isolate non-compliant devices, and integrate seamlessly with broader security frameworks.
Remote Access VPN
Remote access VPNs provide secure connectivity for remote users, extending the corporate network’s security perimeter beyond physical office confines. By encrypting data in transit, these VPNs ensure that remote communications remain confidential and secure from eavesdropping. This function is especially vital in mobile work environments, where employees need reliable access to corporate resources from any location.
In addition to enabling secure remote access, VPNs support compliance with security standards by protecting sensitive data and supporting multi-factor authentication (MFA) measures. By doing so, they ensure that users accessing network resources are authenticated and data integrity is maintained. Remote Access VPNs are integral to continuity planning, enabling business operations during disruptions by allowing employees to work securely.
Network Segmentation
Network segmentation divides a network into smaller, isolated sections to improve performance and security. It allows administrators to apply security controls to each segment, limiting the lateral movement of threats across the network. This isolation is effective in minimizing the potential impact of a security breach, as attackers are confined to a segmented area rather than gaining full network access.
Segmentation also supports compliance by restricting data access based on regulatory requirements. By categorizing devices and users into segments based on function or trust level, organizations can better control access, reduce congestion, and bolster protection against internal and external threats.
Intrusion Prevention Systems (IPS)
Intrusion prevention systems (IPS) actively monitor network traffic for signs of malicious activities, offering protection by preemptively blocking threats. Unlike Intrusion Detection Systems, which only alert administrators of potential breaches, IPS solutions halt malicious activities in real time.
An IPS can be configured to take various actions based on defined security policies, such as blocking source IP addresses, dropping malicious packets, or logging incidents for further analysis. With continuous updates from threat intelligence sources, IPS systems stay ahead of emerging threats and vulnerabilities.
Zero Trust Network Access (ZTNA)
Zero trust network access (ZTNA) is a security model that challenges the traditional perimeter-based security approach by eliminating the notion of implicit trust. ZTNA enforces strict identity verification and access controls at every network layer. Instead of assuming internal network traffic is safe, ZTNA operates on the principle of “never trust, always verify.”
By extending granular security policies and micro-segmentation, ZTNA provides secure access to applications and data both on-premises and in the cloud. This eliminates lateral movement inside the network, a common tactic used in cyber-attacks.
Network Monitoring and Scanning Tools
1. Faddom

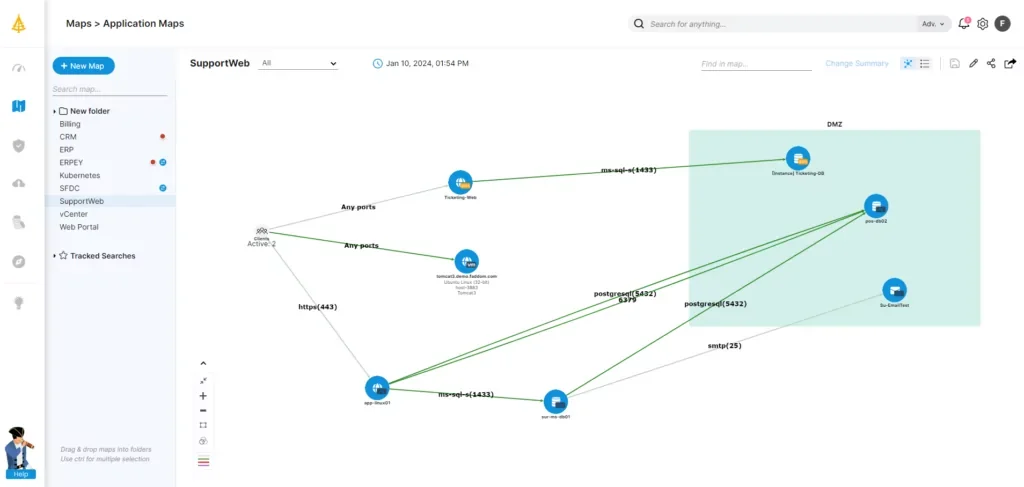
Faddom is an agentless application dependency mapping and anomaly detection platform that helps organizations in securing their networks by identifying hidden risks in real-time. Rather than depending on complex configurations, it automatically maps all servers, applications, and traffic flows across hybrid environments. This enhanced visibility enables IT and security teams to detect risky east-west traffic, shadow IT, and unauthorized connections that traditional perimeter tools may overlook.
Key features include:
- Agentless & Fast Deployment: Complete infrastructure visibility in under 60 minutes without agents or disruptive configurations.
- Real-Time Application Maps: Continuously updated topology maps reveal servers, business apps, and dependencies for accurate documentation and troubleshooting.
- Segmentation & Security: Identify risky traffic patterns and support micro-segmentation strategies to enhance defenses against lateral movement.
- AI-Powered Anomaly Detection: Lighthouse AI detects unusual traffic behaviors, such as DoS attacks and rogue connections, without the need for manual threshold settings.
- Compliance & Governance: Clear visibility into communication flows to help meet security and regulatory requirements.
Discover more on how Faddom can enhance your network security strategy!
2. Nessus Network Monitor

Nessus Network Monitor is a passive network monitoring tool that provides continuous visibility into network activity without active scanning. It inspects live traffic to detect new hosts, services, and vulnerabilities as they appear. By using deep packet inspection and integrating with broader Tenable platforms, it supports real-time exposure detection across dynamic environments.
Key features include:
- Passive network monitoring: Observes network traffic continuously without generating scan traffic or affecting performance
- Real-time asset detection: Identifies new hosts and services as soon as they appear on the network
- Deep packet inspection: Analyzes traffic across multiple protocols to uncover hidden vulnerabilities
- Continuous visibility: Tracks assets and network behavior around the clock without manual intervention.
- Platform integration: Integrates with Tenable Vulnerability Management and Tenable Security Center for consolidated visibility.
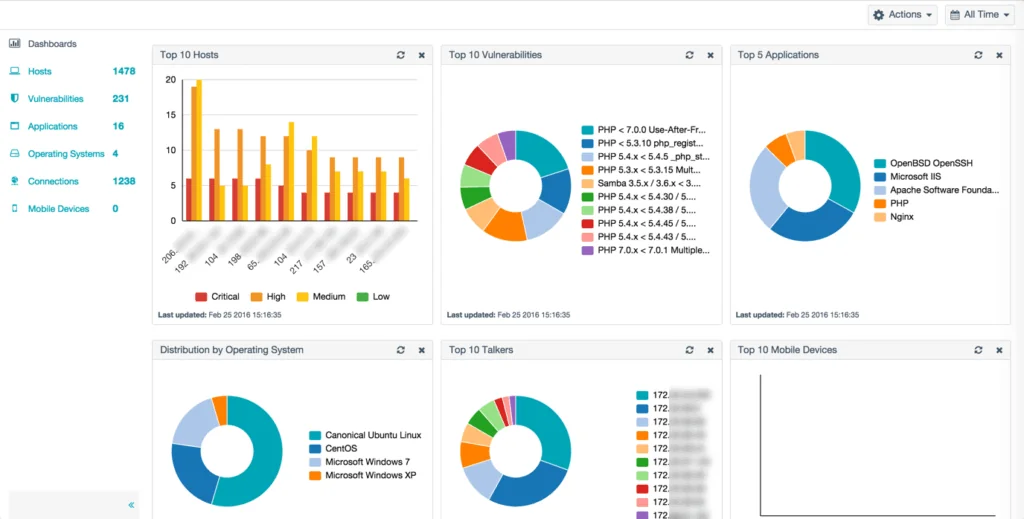
Source: Tenable
3. Wireshark

Wireshark is an open-source network protocol analyzer used for capturing and inspecting network traffic. It enables administrators and security teams to examine packet-level data, troubleshoot connectivity issues, and analyze protocol behavior. Wireshark supports interactive exploration of captured traffic and provides inspection of hundreds of network protocols.
Key features include:
- Packet capture and inspection: Captures live traffic and allows interactive analysis of packets.
- Protocol analysis: Supports deep inspection of hundreds of network protocols.
- Cross-platform support: Available for Windows, macOS, Linux, and other operating systems.
- Open-source licensing: Distributed under the GNU General Public License with publicly available source code.
- Active community support: Maintained by a global community contributing updates and enhancements.
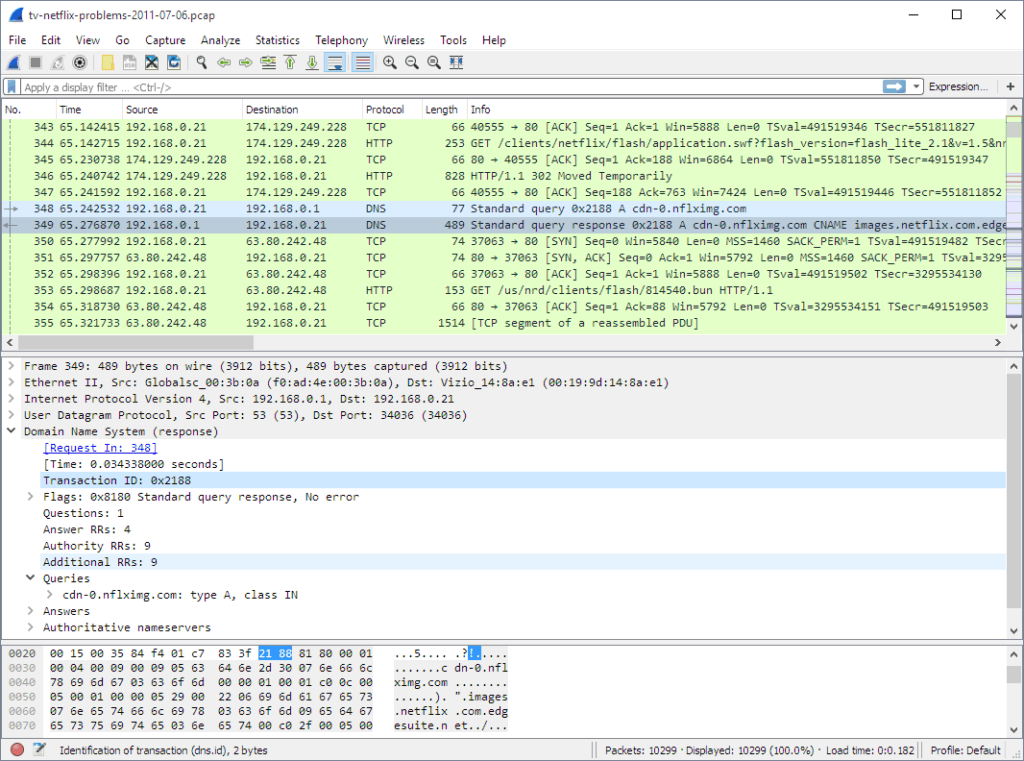
Source: Wireshark
4. Nmap
Nmap is a free and open-source utility for network discovery and security auditing. It uses raw IP packets to identify active hosts, open ports, running services, operating systems, and firewall configurations. Designed for both small and large environments, Nmap supports advanced scanning techniques and includes additional tools for visualization and analysis.
Key features include:
- Host discovery: Identifies active devices on a network using multiple probing techniques
- Port scanning: Supports TCP and UDP scanning methods to detect open ports
- Service and version detection: Determines application names and versions running on hosts
- Operating system detection: Identifies operating systems and device characteristics.
- Extensible scripting engine: Includes the Nmap scripting engine for custom security checks and automation.
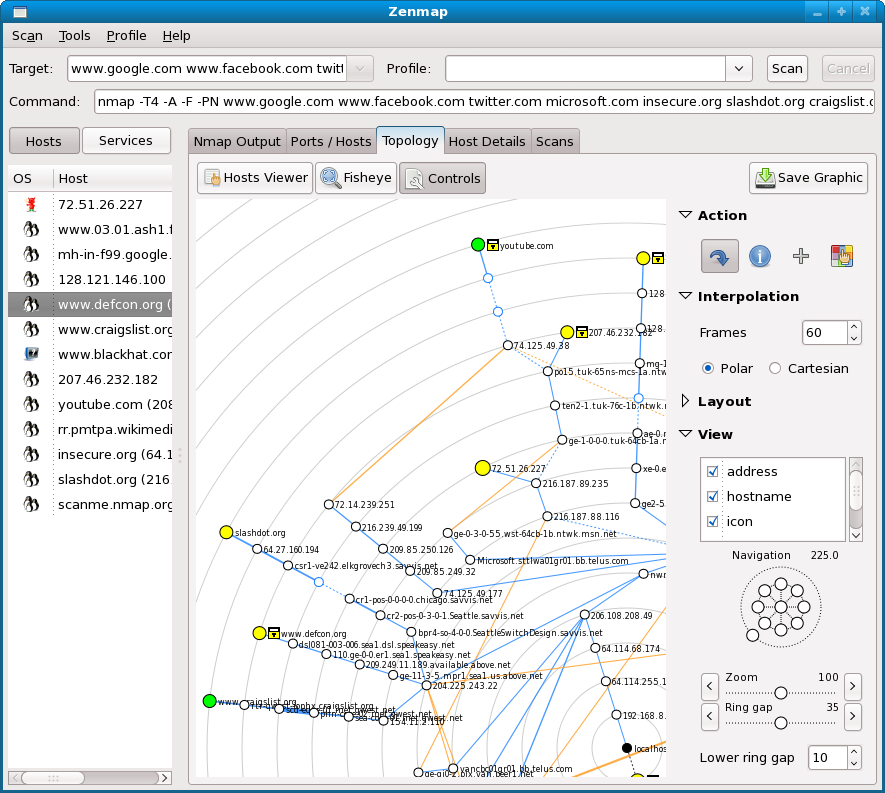
Source: Nmap
5. ZMap

ZMap is an open-source network scanner optimized for large-scale Internet-wide surveys. It is designed to send single packets at high speed to enumerate hosts and services across large address spaces. ZMap is commonly used in research and measurement studies to assess exposure and service availability at scale.
Key features include:
- High-speed scanning: Capable of scanning the entire public IPv4 address space on a single port in under an hour on standard hardware.
- Single-packet architecture: Uses a lightweight scanning model optimized for performance.
- Internet-wide surveys: Designed for large-scale measurement and research use cases.
- Modular ecosystem: Works with related tools such as ZGrab for application-layer scanning and ZDNS for DNS lookups.
- Open-source project: Maintained as part of a broader open-source measurement toolkit.
Network Perimeter Tools
6. Palo Alto Networks NGFW

Palo Alto Networks next-generation firewalls provide application-aware traffic inspection combined with machine learning–driven threat detection. The platform uses inline deep learning to analyze traffic patterns and identify evasive and zero-day threats beyond traditional signature-based methods.
Key features include:
- Inline deep learning inspection: Applies deep learning models directly to traffic flows to detect unknown and evasive threats.
- Zero-delay signature updates: Distributes newly generated threat protections to connected firewalls within seconds.
- IoT device visibility: Profiles connected devices to identify type, vendor, model, and firmware for improved control.
- AIOps-based health monitoring: Uses predictive analytics to monitor firewall health and reduce operational disruptions.
- Unified security architecture: Provides consistent policy enforcement across on-premises, cloud, and container environments.

Source: Palo Alto Networks
7. Fortinet FortiGate
FortiGate next-generation firewalls are designed to secure enterprise, campus, branch, and data center environments. They combine firewalling with advanced security services and integrated management. FortiGate appliances are available in multiple form factors to address different performance and deployment requirements.
Key features include:
- Next-generation firewall capabilities: Combines traditional firewall functions with advanced threat protection.
- Broad deployment options: Supports data center, enterprise campus, branch, and small office environments.
- Integrated security services: Incorporates AI-powered security features within the firewall platform.
- Performance optimization: Uses purpose-built hardware to enhance firewall throughput and efficiency.
- Centralized management support: Simplifies administration across distributed firewall deployments.
Source: Fortinet
8. Cisco Secure Firewall

Cisco Secure Firewall delivers threat protection across data center, cloud, campus, branch, and IoT environments. It integrates with Cisco’s broader security ecosystem and is powered by Talos threat intelligence. The platform emphasizes unified management, encrypted traffic visibility, and zero-trust segmentation across distributed environments.
Key features include:
- Talos threat intelligence integration: Leverages large-scale threat telemetry and machine learning for threat protection
- Encrypted traffic visibility: Detects threats within encrypted traffic without requiring decryption
- Snort-based zero-day protection: Uses the SnortML detection engine to block patterns linked to zero-day attacks
- Unified management: Provides centralized policy and visibility across physical, virtual, and cloud firewalls.
- Hybrid mesh firewall architecture: Supports distributed enforcement across data center, cloud, campus, and IoT networks.

Source: Cisco
9. Snort

Snort is an open-source intrusion prevention system that performs real-time traffic analysis and packet logging. It uses rule-based detection to identify malicious network activity and can operate as a packet sniffer, packet logger, or inline intrusion prevention system. Snort rules are maintained through community and subscriber rule sets, enabling continuous threat coverage.
Key features include:
- Rule-based intrusion detection: Uses predefined and custom rules to detect malicious traffic patterns.
- Inline intrusion prevention: Can block malicious packets in real time when deployed inline.
- Packet sniffing and logging: Captures and logs network traffic for debugging and analysis.
- Community and subscriber rulesets: Provides access to both community-developed and Talos-curated detection rules.
- Open-source deployment: Available for personal and enterprise use with publicly accessible source code.
Source: Snort
Zero Trust and Microsegmentation Tools
10. Zscaler Zero Trust Exchange

Zscaler Zero Trust Exchange is a cloud-based platform that applies zero trust principles to user, workload, and device access by brokering connections based on identity, context, and policy rather than extending network access. It uses a proxy architecture to inspect traffic (including TLS/SSL) and enforce least-privileged access to applications and services.
Key features include:
- Least-privileged access brokering: Establishes one-to-one connections between users (or workloads) and specific applications based on policy.
- Full TLS/SSL inspection at scale: Uses a proxy-based architecture to inspect encrypted traffic for threats and policy violations.
- Attack surface reduction: Hides applications behind the platform to reduce direct internet exposure.
- Lateral movement prevention: Connects authorized entities to apps rather than the broader network to limit internal spread paths.
- Identity and context verification: Integrates with third-party identity providers to verify user, device, and workload identity and apply conditional access.
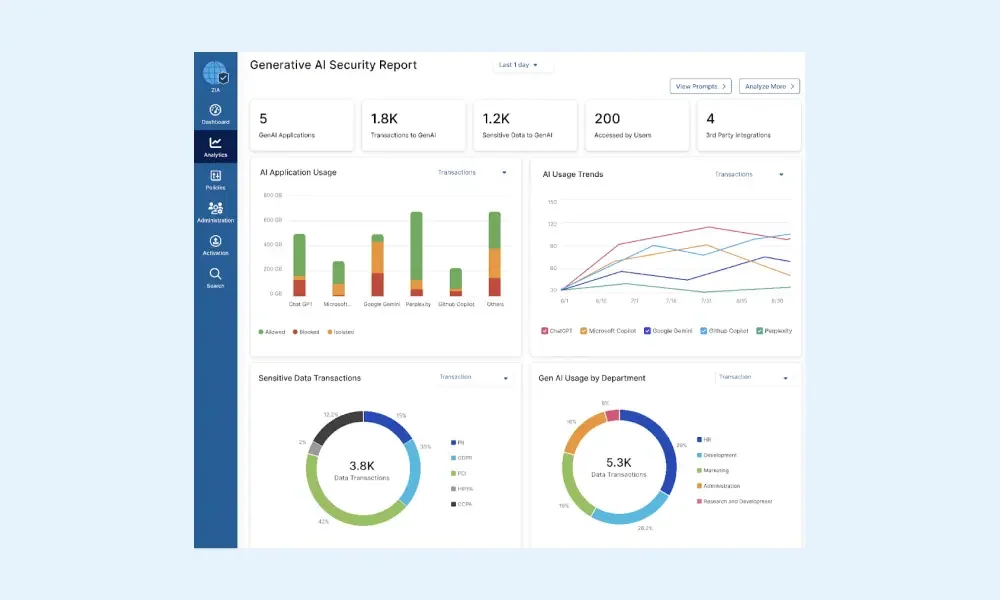
Source: Zscaler
11. Illumio

Illumio is a microsegmentation and breach containment platform to reduce lateral movement by making traffic flows visible and enforcing segmentation policies across hybrid and multi-cloud environments. Its approach focuses on identifying risk, detecting suspicious activity, and applying controls that limit how far an attacker can move once inside an environment.
Key features include:
- Microsegmentation for hybrid environments: Applies segmentation controls across on-premises, multi-cloud, and hybrid workloads.
- Lateral movement risk reduction: Helps prevent or limit east-west spread by enforcing segmentation policy around critical assets.
- Centralized policy visibility and control: Provides a single console to view environments and manage segmentation policies.
- Attack detection and containment workflows: Supports identifying threats and containing them with targeted controls.
- AI security graph foundation: Uses an AI security graph concept to provide context for identifying risk and prioritizing response actions.
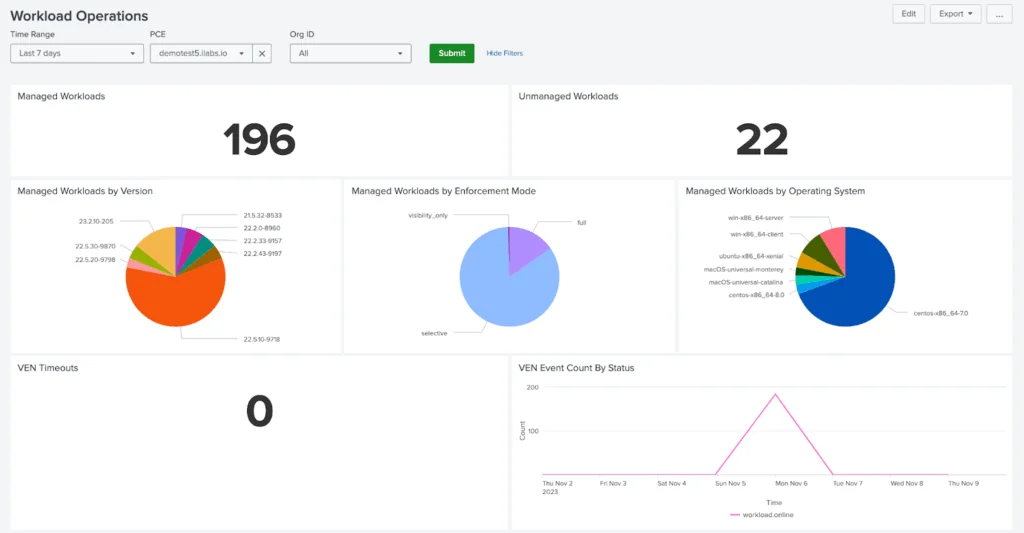
Source: Illumio
12. Akamai Guardicore Segmentation

-
Akamai Guardicore Segmentation is a microsegmentation platform that maps assets and traffic flows, then enables policy creation and enforcement to reduce lateral movement across data centers and cloud environments. It provides visibility at user and process granularity and supports both live and historical analysis to inform segmentation policies and investigations.
Key features include:
- Process-level microsegmentation: Enables granular segmentation controls down to individual processes and services.
- Real-time and historical visibility: Provides current and past activity views to support investigation and forensic analysis.
- Broad platform coverage: Supports segmentation across legacy systems as well as modern cloud and container environments.
- Flexible asset labeling: Uses labeling that can integrate with orchestration systems and CMDB sources for policy grouping.
- Template-based policy creation: Supports faster policy building with templates and workflows for common segmentation use cases.
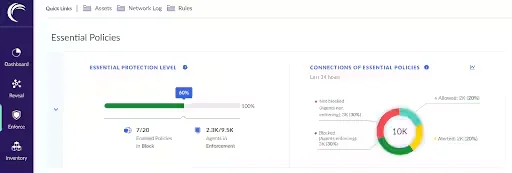
Source: Akamai
Conclusion
As cyber threats continue to grow in complexity and frequency, organizations must adopt a comprehensive, layered approach to network security. By combining advanced technologies, proactive policies, and continuous monitoring, businesses can better defend against both known and emerging threats. A strong network security strategy not only protects critical assets but also ensures regulatory compliance and supports long-term operational resilience.