What Are Ransomware Protection Solutions?
Ransomware protection solutions are comprehensive tools and strategies designed to defend organizations against ransomware attacks. These attacks occur when cybercriminals encrypt an organization’s data and demand payment to restore access.
Ransomware solutions address the full spectrum of the ransomware threat lifecycle, including prevention, detection, response, and recovery. Their main role is to reduce the risk of infection, minimize disruption during an attack, and enable rapid restoration of operations.
Modern ransomware solutions combine multiple layers of protection, such as endpoint security, real-time threat detection, automated backup, privilege control, and incident response. They are frequently updated to counter evolving tactics used by attackers. They also help organizations avoid the severe financial and reputational impacts associated with ransomware incidents.
Table of Contents
ToggleEditor’s note: Updated the article to include recent market data, and updated information about ransomware protection solutions to reflect features and capabilities in 2026.
This is part of a series of articles about Ransomware
Ransomware Protection Market Trends
Key Drivers Shaping the Market
According to recent market research, multiple trends are accelerating demand for ransomware protection technologies. Ransomware-as-a-service ecosystems are one of the most influential drivers. Criminal groups sell ransomware kits and take a percentage of the ransom payment, typically between 10% and 40%, enabling affiliates with limited technical expertise to carry out attacks.
Another major factor is the growth of phishing and targeted breaches. Techniques such as AI-generated voice phishing (“vishing”) make social engineering attacks more convincing and increase the likelihood of credential compromise.
The migration of workloads to cloud and SaaS platforms has also expanded the attack surface. Organizations often struggle to enforce least-privilege access and identity controls across complex cloud environments, creating opportunities for attackers.
Additionally, cyber-insurance requirements are influencing security investments. Insurers increasingly require organizations to implement controls such as multi-factor authentication, network segmentation, and immutable backups before issuing coverage.
Key Features of Ransomware Protection Solutions
Ransomware solutions typically offer the following capabilities.
Real-Time Threat Detection and Prevention
Real-time threat detection and prevention features monitor network traffic, file activities, and user behaviors using advanced technologies such as machine learning, behavioral analytics, and threat intelligence feeds. They can identify suspicious patterns, block known malware signatures, and flag unexpected file encryption before significant damage occurs.
Effective real-time prevention often includes sandboxing, isolating potential threats for analysis, and heuristic scanning, which detects unknown or zero-day ransomware variants. This proactive approach ensures that even new or modified attack techniques don’t bypass security controls.
Endpoint Protection
Endpoint protection secures user devices such as laptops, desktops, smartphones, and servers. These solutions use antivirus engines, exploit prevention modules, and application allowlisting to neutralize payloads before they can trigger encryption. They also block malicious downloads, prevent lateral movement across the network, and manage device security configurations to address vulnerabilities that ransomware often exploits.
This broad coverage ensures consistent application of security controls, even for remote or bring-your-own-device (BYOD) users. By placing security directly at the endpoint, organizations strengthen their overall posture and reduce risk at the most common points of compromise.
Automated Backup and Recovery
Automated backup and recovery solutions continually create copies of critical data and configurations, storing them securely, often offline or in the cloud. Should a ransomware attack occur, organizations can quickly restore clean, uninfected data without succumbing to ransom demands. These systems regularly test backup integrity, ensuring that recovery points are viable and reliable during an emergency.
Schedules and policies are customizable, letting administrators balance recovery point objectives (RPOs) and recovery time objectives (RTOs) to meet business needs. Advanced solutions may offer immutable storage, which protects backup files from being altered or deleted by malware. Automated orchestration further reduces manual steps, enabling rapid, consistent recovery at scale.
Learn more in our detailed guide to ransomware recovery
Access Control and Privilege Management
Access control and privilege management limit ransomware’s impact by enforcing the principle of least privilege: users and applications only have access rights strictly necessary for their tasks. Security solutions monitor account activity, flag privilege escalations, and automatically block risky behaviors such as unauthorized access attempts or credential misuse.
Role-based access, just-in-time privilege elevation, and multifactor authentication (MFA) are key tools within this category. They bolster defense by making it harder for ransomware to exploit compromised credentials or move laterally within a network. Regular audit logs and comprehensive reporting help with compliance requirements.
Incident Response and Containment
Incident response and containment features detect incidents, isolate infected endpoints, and activate playbooks that guide security teams through mitigation steps. Automated containment may involve killing malicious processes, disconnecting systems from the network, or rolling back unauthorized changes, halting the spread of ransomware before encryption completes.
Integration with ticketing systems, SIEM platforms, and threat intelligence sources allows for a coordinated incident response. Rapid communication and reporting enable incident teams to analyze attacks, identify their origin, and initiate remediation. Post-incident forensics and root cause analysis further strengthen long-term resilience.
Notable Ransomware Protection Solutions
1. Faddom

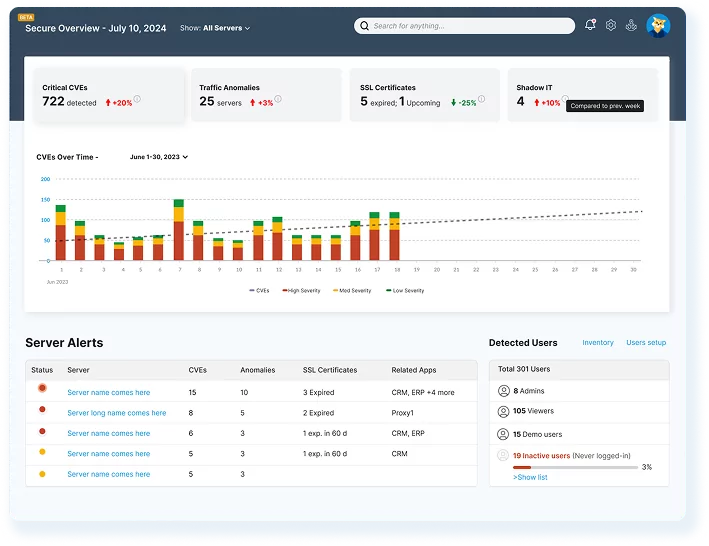
Faddom enhances ransomware protection by providing complete, real-time visibility into all application and server dependencies across on-premises, hybrid, and multicloud environments with application dependency mapping. By automatically mapping east-west and north-south traffic, it enables organizations to identify vulnerable connections, shadow IT, and unexpected communication paths before attackers can exploit them.
In the event of a ransomware incident, Faddom acts as a dynamic blueprint of your IT environment. This allows teams to isolate affected systems, verify clean recovery points, and restore services without any guesswork. Its agentless, continuous discovery process ensures that the maps are always accurate, supporting prevention, response, and post-attack analysis.
Key features include:
- Agentless and continuous discovery: Map your entire environment safely in under 60 minutes without installing agents or disrupting operations.
- Hybrid and multicloud coverage: Unify visibility across on-premises, virtual, and cloud infrastructures for a complete defense picture.
- Real-time dependency mapping: Instantly visualize how ransomware could spread across interconnected systems.
- Security posture enhancement: Detect risky lateral movement paths and unauthorized services before attackers do.
- Incident containment and recovery: Identify impacted servers and validate dependencies for faster, safer restoration.
- AI-powered anomaly detection: Faddom’s Lighthouse AI flags unusual traffic and behavioral patterns, enabling faster containment before systems are encrypted.
Book a demo to get your live dependency map in under an hour!
2. NinjaOne

NinjaOne is a unified IT operations platform that combines endpoint management, monitoring, and security capabilities. It centralizes visibility across devices and enables automation of IT tasks, helping organizations detect and respond to threats more efficiently. Its approach focuses on reducing tool sprawl while improving operational control and resilience.
Key features:
- Unified endpoint management: Provides centralized control and visibility across devices from a single interface.
- Automated patch management: Keeps systems updated to reduce vulnerabilities that ransomware can exploit.
- Backup and recovery: Enables data protection and restoration capabilities to support recovery after attacks.
- AI-driven automation: Automates IT operations and security workflows to improve response times.
- Integrated monitoring and management: Combines device monitoring, remote management, and security controls in one platform.
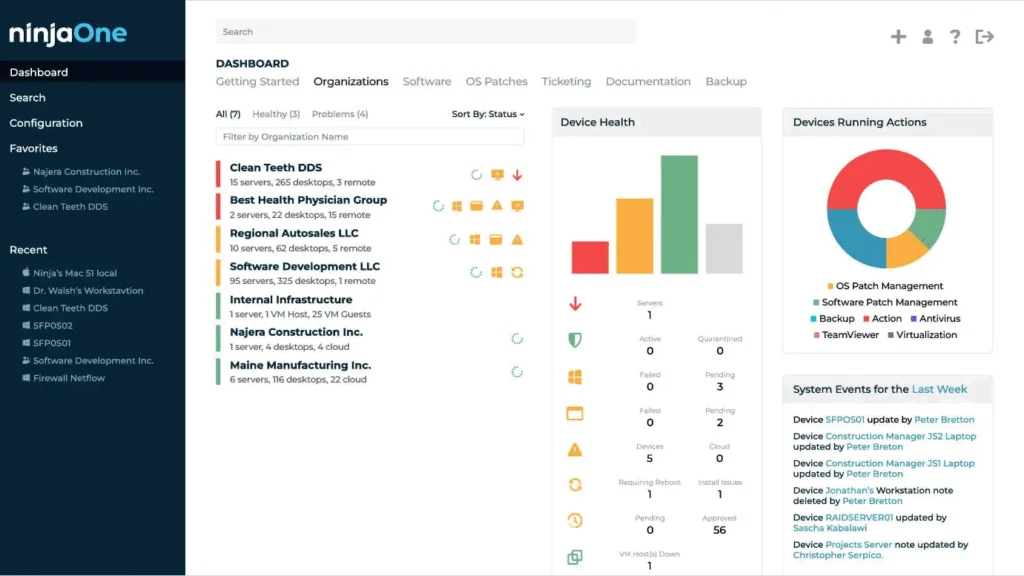
Source: NinjaOne
3. ManageEngine

ManageEngine provides a set of IT management and security tools that cover identity, endpoints, networks, and applications. Its platform integrates monitoring, analytics, and security capabilities, allowing organizations to manage infrastructure while detecting threats and ensuring compliance across environments.
Key features:
- IT operations monitoring: Tracks network, server, and application performance to identify anomalies and potential threats.
- Identity and access management: Controls user access with capabilities such as MFA, SSO, and privileged access management.
- Security information and event management: Aggregates logs, detects threats, and supports incident response processes.
- Unified endpoint management: Secures and manages desktops, servers, and mobile devices from a central platform.
- AI-powered analytics: Provides insights and correlation across IT data to improve detection and decision-making.
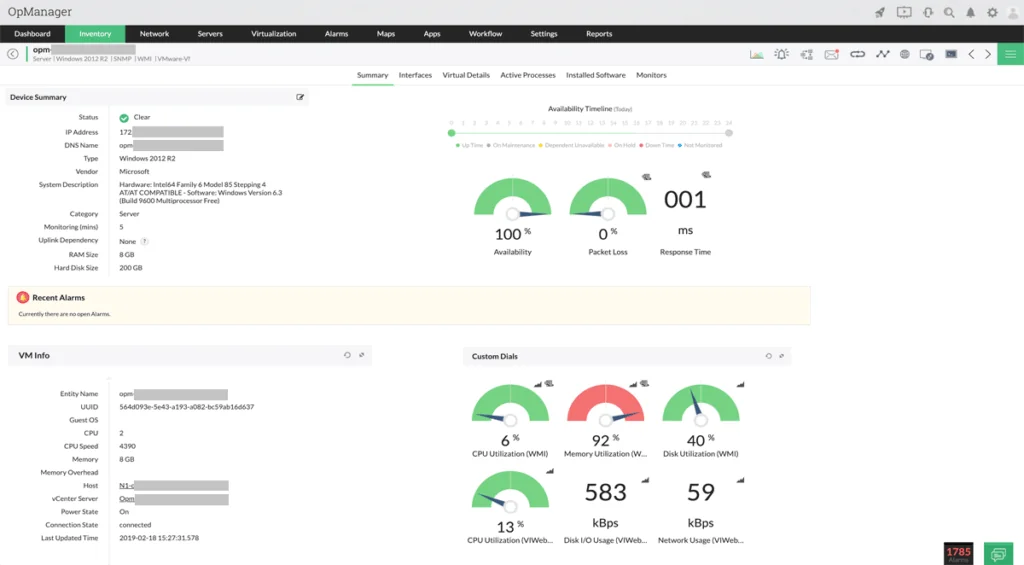
Source: ManageEngine
4. Fortra
Fortra focuses on data-centric security, aiming to protect sensitive information across endpoints, networks, and cloud environments. Its solutions address risk detection, threat prevention, and security gap identification, helping organizations strengthen their overall cybersecurity posture.
Key features:
- Data protection and classification: Identifies and secures sensitive data across environments.
- Threat detection and prevention: Helps identify and stop phishing, impersonation, and other attack vectors.
- Security gap analysis: Detects vulnerabilities and weaknesses before they are exploited.
- Offensive security capabilities: Simulates attacks to expose weaknesses and improve defenses.
- Support for secure AI adoption: Addresses risks related to AI usage and data ex
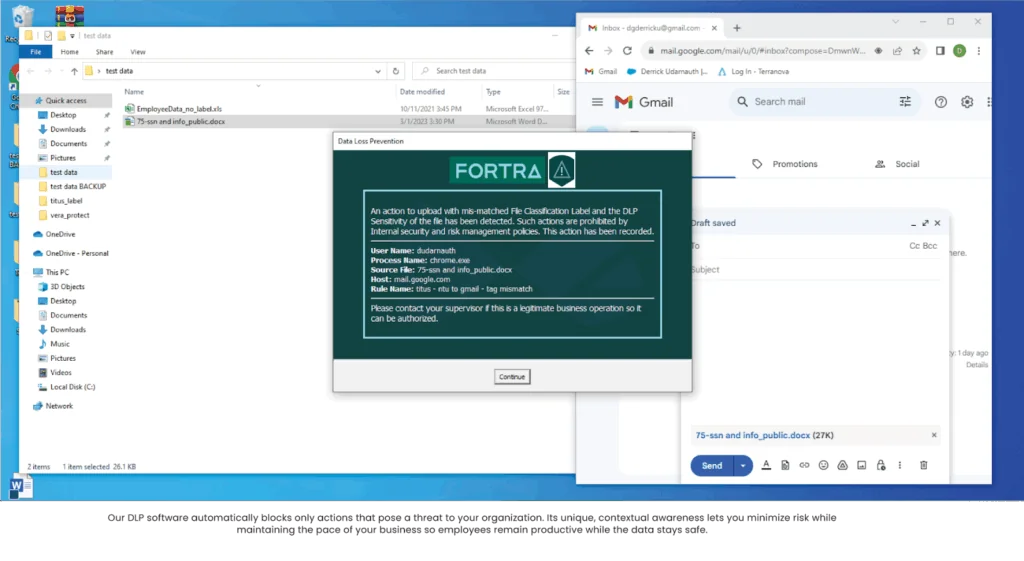
Source: Fortra
5. Malwarebytes

Malwarebytes is a cybersecurity solution focused on protecting endpoints from malware, ransomware, and online threats. It combines real-time threat detection with additional capabilities such as web protection, privacy tools, and identity monitoring to reduce exposure to attacks.
Key features:
- Real-time threat protection: Detects and blocks malware, ransomware, and exploits as they occur.
- Web protection and scam blocking: Prevents access to malicious websites and harmful downloads.
- Multi-device security: Protects desktops, mobile devices, and tablets across environments.
- Privacy and identity protection: Includes VPN, tracking protection, and identity monitoring capabilities.
- Lightweight endpoint security: Runs in the background with minimal performance impact while maintaining protection.
Source: Malwarebytes
Endpoint Security Solutions with Ransomware Protection
6. Acronis

Acronis Cyber Protect is an integrated platform that combines endpoint protection, detection and response, and data protection capabilities. It brings together security and backup functions, allowing organizations to both prevent attacks and recover data using a single system.
General features:
- Integrated protection platform: Combines cybersecurity, backup, disaster recovery, and management capabilities in one solution.
- EDR and XDR capabilities: Supports detection, investigation, and response across endpoints and workloads.
- Centralized management: Provides a web-based console for managing security operations and multiple environments.
- Automation and integrations: Includes prebuilt integrations and automation for IT and security workflows.
Ransomware protection features:
- Threat detection and response: Identifies and responds to malicious activity across systems using EDR/XDR.
- Backup-based recovery: Enables restoration of data and systems after ransomware incidents.
- Resilience across environments: Protects physical, virtual, and cloud workloads from ransomware impact.
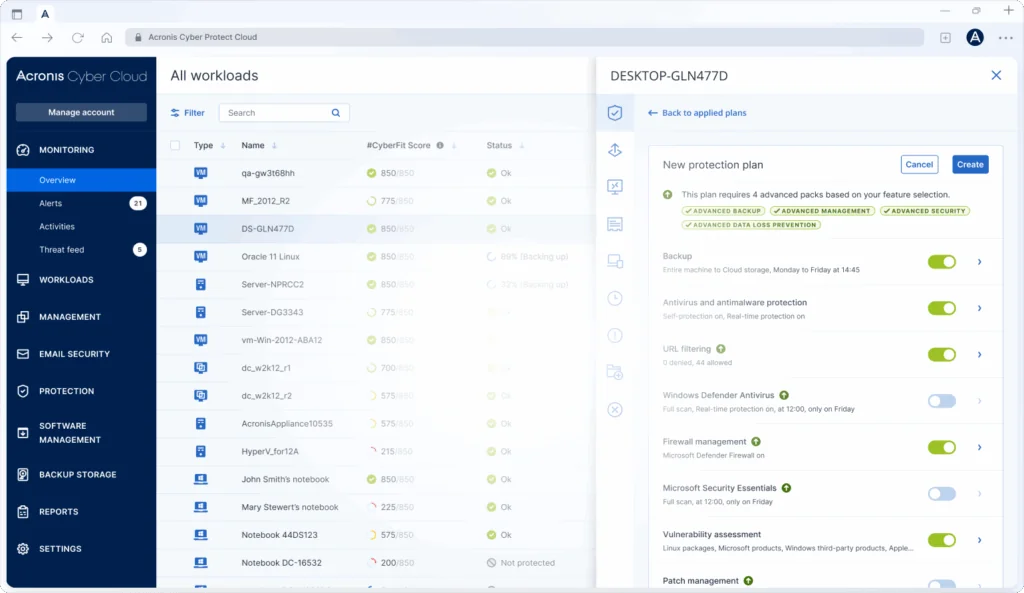
Source: Acronis
7. CrowdStrike Falcon

CrowdStrike Falcon is a cloud-native endpoint security platform that uses AI and threat intelligence to detect and respond to advanced attacks. It focuses on identifying attacker behavior and automating response actions across endpoints.
General features:
- AI-powered detection: Uses machine learning and behavioral analysis to identify threats, including malware-free attacks.
- Lightweight single agent: Deploys a unified sensor across endpoints for visibility and protection.
- Adversary intelligence: Leverages threat intelligence to detect sophisticated attack techniques.
- Automated investigation and response: Uses AI to triage alerts and automate incident response workflows.
- Cross-domain visibility: Correlates activity across systems to detect lateral movement and complex attacks.
Ransomware protection features:
- Behavior-based ransomware detection: Identifies ransomware activity without relying on signatures.
- Automated containment: Stops malicious processes and limits spread during an attack.
- High-accuracy detection: Designed to detect and block ransomware with minimal false positives.
Source: CrowdStrike
8. Sophos Endpoint

Sophos Endpoint is an AI-driven endpoint protection solution that combines prevention, detection, and response capabilities. It provides centralized management and automated remediation, with specific mechanisms to detect and reverse ransomware activity.
General features:
- AI-powered threat prevention: Blocks a wide range of threats before execution.
- EDR and XDR capabilities: Supports threat hunting, investigation, and response across endpoints.
- Centralized cloud management: Uses a cloud-based console to monitor alerts and manage policies.
- Automated response: Adapts remediation actions based on the context of detected threats.
Ransomware protection features:
- CryptoGuard technology: Detects malicious encryption by monitoring file behavior.
- Automatic file rollback: Restores files affected by ransomware to their original state.
- Remote ransomware protection: Defends against attacks originating from other devices on the network.
- Boot record protection: Prevents ransomware from corrupting system boot components.
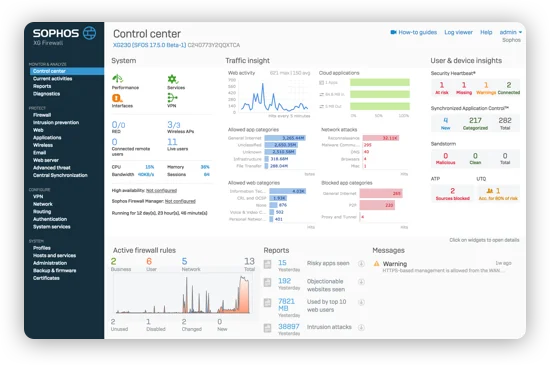
Source: Sophos
9. SentinelOne Singularity
SentinelOne Singularity is an AI-based security platform that provides unified protection across endpoints, cloud workloads, and identities. It focuses on real-time detection and automated response using autonomous technologies.
General features:
- Unified security platform: Provides visibility and control across endpoints, cloud, and data.
- Real-time detection and response: Uses AI to detect and respond to threats as they occur.
- Threat intelligence integration: Correlates data for investigation and analysis.
- Broad workload coverage: Supports containers, virtual machines, servers, and hybrid environments.
Ransomware protection features:
- AI-powered runtime protection: Detects and blocks attacks during execution.
- Autonomous response: Automatically contains and mitigates threats without manual intervention.
- Attack path analysis: Identifies how threats propagate and prioritizes remediation.
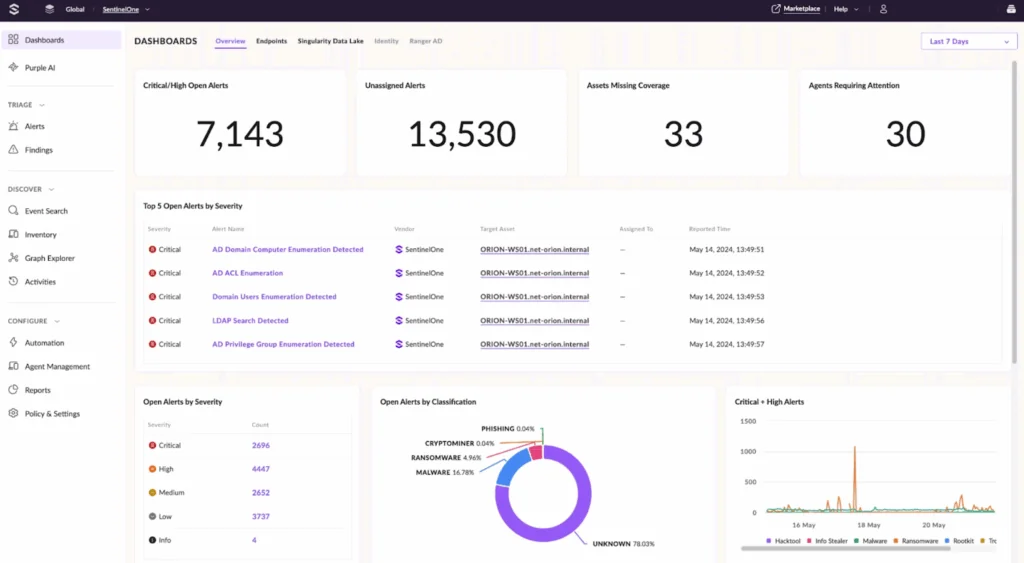
Source: SentinelOne
10. Spin.ai

Spin.ai provides SaaS-focused security that combines backup, posture management, and ransomware protection. It is intended to secure cloud applications and enable fast recovery from data loss or attacks.
General features:
- Unified SaaS security platform: Protects multiple SaaS applications from a single interface.
- Security posture management: Detects misconfigurations and enforces security policies.
- AI-driven risk assessment: Evaluates third-party apps and user activity to identify risks.
- Browser and access controls: Monitors extensions and access to prevent data leakage.
Ransomware protection features:
- Ransomware detection and response: Identifies malicious activity in SaaS environments and isolates affected data.
- Automated backups: Performs frequent backups to ensure data availability.
- Rapid recovery: Restores clean data quickly to minimize downtime after an attack.
- Attack containment: Limits the spread of ransomware within SaaS environments.
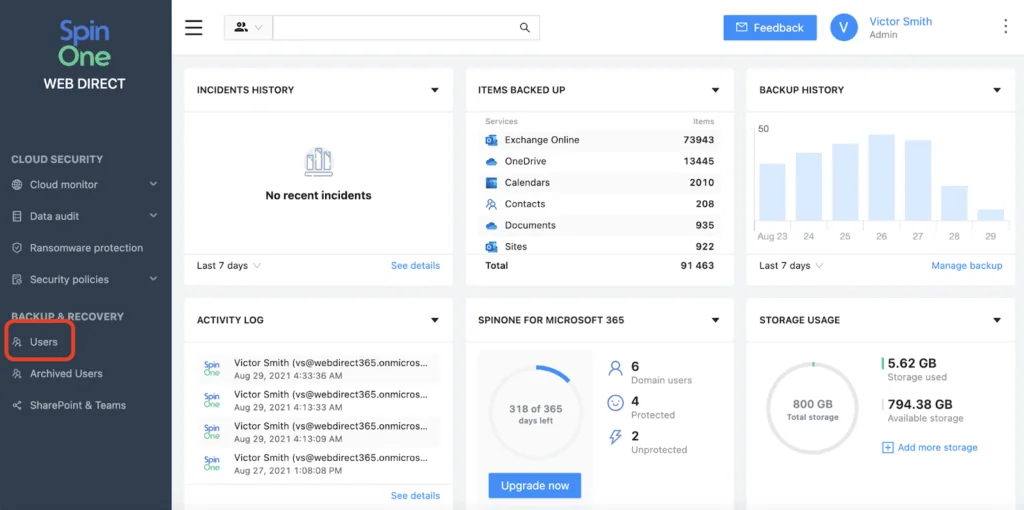
Source: Spin.AI
Conclusion
Ransomware solutions provide layered protection that spans prevention, detection, containment, and recovery. By combining technologies such as behavioral monitoring, automated response, and resilient backup, they minimize the impact of attacks while enabling rapid restoration of business operations. As ransomware tactics continue to evolve, adopting a multi-faceted defense strategy ensures that organizations can maintain resilience, protect critical data, and reduce downtime in the face of ongoing threats.