Network insights are essential to keep things running smoothly. Just as a smart mechanic can learn a lot by looking (and listening) under the hood of a car, network monitoring platforms and protocols let IT teams collect data from a wide range of network devices, such as routers, switches, and servers, to help optimize network performance, facilitate troubleshooting, and even prevent problems before they can occur.
Network monitoring also helps organizations meet industry regulations to monitor networks for security and performance and also leverage alerting capabilities to prevent unauthorized access to their data and systems.
Maintaining productivity and saving money by minimizing downtime and data loss is yet another key benefit of network monitoring.
One of the main ways that IT managers collect data from network devices is by using the Simple Network Management Protocol (SNMP), a standard communications protocol for monitoring and managing networks.
But as with most things in the tech world, technological advances sometimes leave businesses running older systems in the dust. Even if an IT department is already using SNMP, they may be running an older version, SNMP v2, and thus missing out on the many advantages delivered by the updated version, SNMP v3.
In this post, we’ll explore SNMP before outlining some of the advantages of SNMP v3 and why it’s probably time for an upgrade. We will also cover expert tips for getting past some of the speed bumps organizations may encounter along the way.
What Is SNMP and How Does It Help You?
SNMP is one of the best-known protocols. Based on UDP, one of the simplest and most universal networking protocols, it allows admins to configure and extract device and performance data from a wide range of network devices, including switches, routers, firewalls, printers, and servers.
An SNMP network typically consists of a manager that updates data or requests data from agents on each device within the network. Agents store data in a management information base (MIB) and then receive and respond to SNMP events. Responses from the agent to the manager, which include data from the MIB, are also known as “traps.”
SNMP Versions
SNMP was created in 1988 by the Internet Engineering Task Force (IETF). It is today practically universal and available for almost every platform and device companies could possibly have on their network.
Different versions of SNMP have been released over the years, adding major improvements to the original design. However, not all SNMP versions are backwards compatible.
SNMP version 2, introduced in 1993, added a number of basic features and functionalities, giving the protocol a more significant role in network monitoring and management.
SNMP version 3, introduced in 2002, added several major improvements, especially enhanced security features. SNMPv3 was created primarily to close many security gaps in earlier versions. However, although it has been around for over 20 years, for several reasons, many organizations are still using SNMPv2.
This is due, in part, to legacy systems and the complexity of transitioning, although some resistance may come from a lack of knowledge or awareness on the part of IT teams. However, as we will see in the next section, SNMPv3’s security features make it the only reasonable choice for most modern businesses.
Let’s look at some of the differences between the two versions as well as some essential points to help organizations clear the hurdles involved in transitioning to SNMPv3.
SNMP v2 vs SNMP v3: What Are the Main Differences?
While SNMPv3 is the latest version, it’s not exactly brand-new. As already mentioned, it’s been over 20 years since it was released, meaning many IT professionals were barely toddlers when it first came out.
So why isn’t everybody using it yet?
SNMPv3 does have some drawbacks, namely its complexity and the difficulty of transitioning from one protocol to another. Here are some of the key differences between SNMPv2 and SNMPv3:

A Modern Approach to Security
The greatest advantage of SNMPv3, by far, is its vastly improved security features. SNMPv2 offered no encryption or authentication. In SNMPv1 and SNMPv2, passwords were sent as a community string in clear text between managers and agents, leaving huge gaps in security.
First, the SNMP community string is a single identifier, unlike modern systems, which are based on a username and password. Further, many SNMP-compatible devices come with a pre-configured (hard-coded) community string, giving any user with this information access to critical device configuration parameters. Without encryption on the community string, it can be read by anyone able to intercept network information, such as through packet sniffers.
Why Is SNMP Security Important?
While SNMP only transmits information about network devices, which wouldn’t seem to be as sensitive as other types of data (such as credit card or personal health information), it can be very useful to attackers. IP addresses, subnet masks, gateways, device statuses, and events can help attackers identify vulnerable devices and gain access. Once inside the organization’s network, they can then take control of other systems and cause tremendous harm.
The Security Edge of SNMP v3
Therefore, SNMPv3 introduced a number of security enhancements. While it retains the simplicity of the previous model, SNMPv3 allows for modern username and password-based authentication when connecting to an SNMP server. It also allows for encryption of data being transmitted over the network to prevent interception. Finally, SNMPv3 also runs checks to ensure that received data hasn’t been tampered with in transit.
With support for multiple security levels, SNMPv3 contains further safeguards to ensure that the manager and the agent are who they say they are, preventing data from being intercepted and read by attackers (or anyone without the right authorization level).
But the downside of all these improvements is that SNMPv3 can be a lot harder to configure. And because of compatibility issues, it can be challenging to upgrade, which explains why many organizations are still using SNMPv2 despite its massive security flaws.
Transitioning from SNMP v2 to SNMP v3
Although configuring SNMPv3 can certainly pose difficulties, it is by far a better, more secure protocol to use on public and internet-facing devices.
Of course, SNMPv3 isn’t the only alternative today. Some organizations do consider moving from SNMPv2 to a different system altogether—such as telemetry, which offers more sophisticated runtime observability features. However, these systems add unnecessary complexity and expense, which isn’t needed for many network applications.
SNMPv3 remains the simplest, safest option for a wide range of applications, particularly for:
- Retrieving relatively static data, e.g., inventory or neighboring devices
- Dealing with significant numbers of legacy devices that don’t support telemetry
- Collecting nonperformance data, e.g., routing peers, bridge domain neighbors, NTP peers, and device inventory information
Organizations still using SNMPv2 may be hesitant about transitioning to SNMPv3. Here are some of the main reasons many will want to move this to the top of their operations’ priority list.
- Security: This is the #1 reason, as SNMPv2 leaves systems inherently vulnerable.
- Efficiency: SNMPv3 transmits only the data requested, rather than the entire device status.
- Interoperability: SNMPv3 works better with modern devices along with other protocols.
- Simplicity: SNMPv3 makes it easier to implement modern network configurations and meet compliance best practices.
Let’s explore some of the main challenges and solutions when it comes to transitioning from SNMPv2 to SNMPv3.
Device and Platform Compatibility
If legacy hardware or existing network management systems and tools do not support SNMPv3, there are a few options. Device firmware can be updated, or the device can simply be replaced. For software, companies will need to determine if there’s a way to reconfigure it to work with SNMPv3 or upgrade to a modern software solution.
Sometimes, IT departments are reluctant to even begin a change project like this because they’re unaware of what systems and devices are on their network. A tool that facilitates network discovery will provide a big-picture view of their entire network to assess each device and platform for compatibility with SNMPv3. This enables teams to anticipate and prevent problems long before the transition is even started.
Complexity of Configuration
It’s certainly true that SNMPv3 introduces more security configuration options. This creates a steeper learning curve in general to understand and configure security levels and options in SNMPv3, especially as an incorrect configuration could lead to downtime and/or network disruptions.
In addition, migrating SNMPv2 monitoring environments to SNMPv3 could involve time-consuming data mapping and transfer of tasks. Again, understanding the existing system before transitioning to SNMPv3 is critical, as is ensuring training for all responsible IT staff.
The trade-off for this effort is tighter network security, an area where no business should ever have to compromise. In addition, the ongoing, day-to-day administrative burden of SNMPv3, once the transition is complete, will likely be minimal.
Cost of Implementation
One final speed bump is the price tag. In addition to the software and hardware cost to implement SNMPv3, IT staff must be up to speed on all security features and authentication mechanisms, as well as be able to configure systems correctly and maintain them as needed. This is not cheap.
In addition, businesses need to plan ahead for additional IT personnel and resources before and during the transition. Rigorous testing is time-consuming and diverts IT teams and resources from other tasks; however, this step is essential to ensure that SNMPv3 functions correctly and allows for a smooth flow of network operations. Furthermore, during the actual transition period, managing a mixed environment of SNMPv2 and SNMPv3 devices could pose monitoring and security challenges that organizations need to be aware of.
Final Tips
Overcoming all of the above challenges in transitioning from SNMPv2 to SNMPv3 is possible and can even be simplified with careful planning. Here are a few additional tips.
Make sure to choose devices that support SNMPv3; since it’s been around so long, many probably do already, particularly with the latest firmware.
Also, ensure that network management software supports SNMPv3 or choose a platform that does.
Finally, before beginning the transition, get a full picture of existing infrastructure using a network application dependency mapping tool. This allows for proper planning so companies can head off any unforeseen consequences of the transition.
Faddom: Your Key to Network Dependency Mapping and a Smooth Transition to SNMP v3
SNMPv3 is far and away the most secure and efficient version of SNMP. With attacks on the rise against businesses in every single industry, choosing to secure your networks is no longer optional, and SNMPv3 is becoming increasingly popular due to its balance between enhanced security features and simplicity.
While it is an older protocol, SNMPv3 is holding its own against the complexity of modern tools such as telemetry, particularly on systems that do not demand real-time observability.
If you’re looking for a proven, secure, and efficient way to monitor and manage your network, SNMPv3 may be just what you need. And although there can be pitfalls that accompany the transition, going in with your eyes open will make the entire process simpler.
This includes taking the time to map your network and application dependencies prior to making any changes—giving yourself the greatest chance of success.
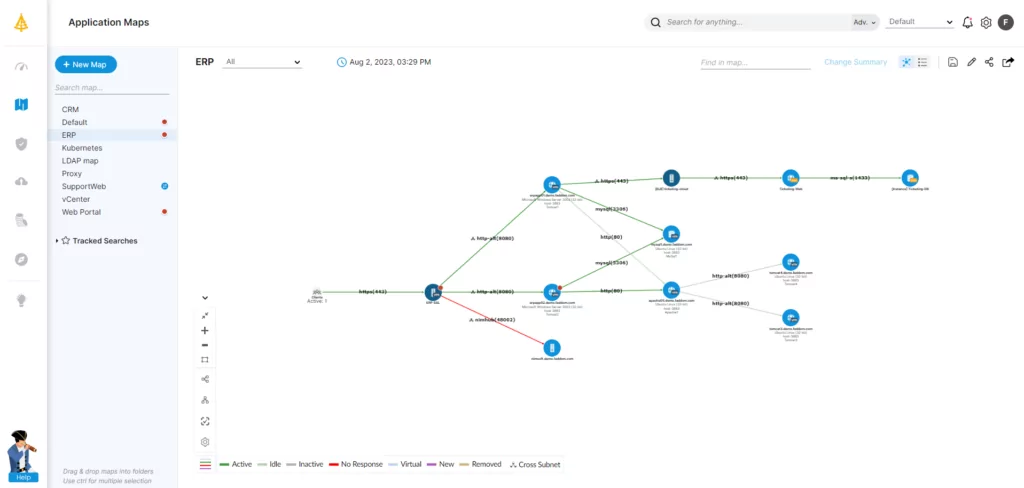
In as little as an hour, Faddom gives you a complete map of your entire network topology, on-premises and cloud, including servers, applications, and dependencies. It’s completely automatic and requires no agents or firewall changes.
With a clear picture of what’s really going on in your network, you’ll be able to manage your network environment’s day-to-day and have the big-picture awareness you need before making any significant changes, such as upgrading to SNMPv3.
To start a free trial and see how simple it can be to get the data you need, just fill out the form on this page.




